|
OpenSSL v. 1.0.0t (runtime, 4/12/2015) |
|
|
 hobbes.nmsu.edu/download/pub/os2/util/encrypt/openssl-1.0.0t-os2knix-20151204-runtime.zip hobbes.nmsu.edu/download/pub/os2/util/encrypt/openssl-1.0.0t-os2knix-20151204-runtime.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0t (toolkit, 4/12/2015, T. Ebisawa) |
|
|
 hobbes.nmsu.edu/download/pub/os2/util/encrypt/openssl-1.0.0t-os2knix-20151204-dev.zip hobbes.nmsu.edu/download/pub/os2/util/encrypt/openssl-1.0.0t-os2knix-20151204-dev.zip |
|
|
OpenSSL v. 1.0.0s (toolkit, 12/6/2015) |
Readme/What's new |
OpenSSL-1.0.0s development kit for OS2-KNIX (kLIBC). Requires OS/2 Warp V4 fix5 or later, TCP/IP for OS/2, kLIBC 0.6.3, gcc 3.3.5 csd3. |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0s-os2knix-20150612-dev.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0s-os2knix-20150612-dev.zip |
|
|
OpenSSL v. 1.0.0s (runtime, 12/6/2015) |
Readme/What's new |
OpenSSL-1.0.0s runtime kit for OS2-KNIX (kLIBC). Requires OS/2 Warp V4 fix5 or later, TCP/IP for OS/2, kLIBC 0.6.3. |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0s-os2knix-20150612-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0s-os2knix-20150612-runtime.zip |
|
|
OpenSSL v. 1.0.0r (toolkit, 20/3/2015) |
Readme/What's new |
OpenSSL-1.0.0o development kit for OS2-KNIX (kLIBC). Requires OS/2 Warp V4 fix5 or later, TCP/IP for OS/2, kLIBC 0.6.3, gcc 3.3.5 csd3. |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0r-os2knix-20150320-dev.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0r-os2knix-20150320-dev.zip |
|
|
OpenSSL v. 1.0.0r (runtime, 20/3/2015) |
Readme/What's new |
OpenSSL-1.0.0o runtime kit for OS2-KNIX (kLIBC). Requires OS/2 Warp V4 fix5 or later, TCP/IP for OS/2, kLIBC 0.6.3. |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0r-os2knix-20150320-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0r-os2knix-20150320-runtime.zip |
|
|
OpenSSL v. 1.0.1k (11/1/2015) |
Readme/What's new |
OpenSSL v1.0.1k for OS/2. Includes binaries and diff. |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.1k-os2-20150111.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.1k-os2-20150111.zip |
|
|
OpenSSL v. 1.0.0p (tookit, 9/1/2015, lpproj) |
Readme/What's new |
OpenSSL-1.0.0o development kit for OS2-KNIX (kLIBC). Requires OS/2 Warp V4 fix5 or later, TCP/IP for OS/2, kLIBC 0.6.3, gcc 3.3.5 csd3. |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0p-os2knix-20150109-dev.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0p-os2knix-20150109-dev.zip |
|
|
OpenSSL v. 1.0.0p (runtime, 9/1/2015) |
Readme/What's new |
OpenSSL-1.0.0o runtime kit for OS2-KNIX (kLIBC). Requires OS/2 Warp V4 fix5 or later, TCP/IP for OS/2, kLIBC 0.6.3. |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0p-os2knix-20150109-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0p-os2knix-20150109-runtime.zip |
|
|
OpenSSL v. 1.0.0o (16/10/2014) |
Readme/What's new |
2014-10-16
- openssl 1.0.0o |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0o-os2knix-20141016-dev.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0o-os2knix-20141016-dev.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0o (runtime, 16/10/2014) |
Readme/What's new |
2014-10-16
- openssl 1.0.0o |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0o-os2knix-20141016-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0o-os2knix-20141016-runtime.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0n (7/8/2014) |
Readme/What's new |
2014-08-07
- openssl 1.0.0n |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0n-os2knix-20140807-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0n-os2knix-20140807-runtime.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0n (toolkit, 7/8/2014) |
Readme/What's new |
2014-08-07
- openssl 1.0.0n |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0n-os2knix-20140807-dev.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0n-os2knix-20140807-dev.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8za (emx, 6/6/2014) |
Readme/What's new |
OpenSSL 0.9.8za experimental port
for genuine EMX (OS2-EMX)
and klibc 0.6.x (OS2-KNIX).
System Requirement
------------------
Runtime (OS2-KNIX):
- OS/2 Warp V4 or later
- Pentium or above CPU
- 32 bit TCP/IP for OS/2 (TCPIP32)
- kLIBC 0.6.x (0.6.3 or later)
Runtime (OS2-EMX):
- OS/2 Warp V3 or later
- i486 or above CPU
- TCP/IP for OS/2
- EMX runtime (0.9d fix 04)
(Note zlib 1.2.7 has linked statically with runtime DLLs.)
Development Kit:
- (OS2-KNIX) gcc 3.3.5 or later
- (OS2-EMX) gcc 2.8.1
- zlib (1.2.8)
Quick and Dirty Installation (OS2-KNIX)
---------------------------------------
Runtime:
1. unzip runtime zip into some directory.
2. add '(the directory)\bin' to PATH
3. add '(the directory)\dll' to LIBPATH
4. set the environment variable OPENSSL_CONF to point 'ssl/openssl.cnf'
set OPENSSL_CONF=(the directory)\ssl\openssl.cnf
(I have no idea about which is the best directory for end-users (non-developer)
to install runtime.
some ideas... e.g.
/usr/local (openssl default configuration)
/usr (commonly unix style)
/etc (some unix style)
/MPTN/ETC (some unix style, a la OS/2)
/extras (Paul Smedley's bldenv)
/openssl (unique directory for openssl)
x:\OS2 (installed as OS2/eCS `system' components)
It is supposed the development kit will be installed into the
directory /extras, bacause this package is configured with '--prefix=/extras'.
)
Quick and Dirty Installation (OS2-EMX)
---------------------------------------
Runtime:
- copy os2_dll\openssl.exe into \emx\bin.
- copy os2_dll\*.dll into \emx\dll.
Development kit:
- copy os2_include\* into \emx\include.
- copy os2_dll\*.a and os2_dll\*.lib into \emx\lib.
How to build runtime DLLs and libraries
---------------------------------------
Prerequisites:
- EMX runtime and development kits
- perl
- grep
- sed
- Unix style shell sh.exe
- GNU make
- Unix style utilities: cp, mv, rm (and more, maybe)
- NetLabs gcc 3.3.5 or later (OS2-KNIX)
- Unix style patch to apply *.diff
Configuration and Make (OS2-EMX):
on OS/2 command prompt:
> os2\OS2-EMX default
> make -f OS2-EMX-DLL.mak
Configuration and Make (OS2-KNIX):
on OS/2 command prompt:
> os2\OS2-KNIX default
> make -f OS2-KNIX-DLL.mak
(and see INSTALL.OS2 in official OpenSSL package.) |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8za-os2emx-20140606.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8za-os2emx-20140606.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0m (6/6/2014, lpproj) |
Readme/What's new |
2014-06-06
- openssl 1.0.0m |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0m-os2emx-20140606.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0m-os2emx-20140606.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8za (toolkit, 6/6/2014) |
Readme/What's new |
OpenSSL 0.9.8za experimental port
for genuine EMX (OS2-EMX)
and klibc 0.6.x (OS2-KNIX).
System Requirement
------------------
Runtime (OS2-KNIX):
- OS/2 Warp V4 or later
- Pentium or above CPU
- 32 bit TCP/IP for OS/2 (TCPIP32)
- kLIBC 0.6.x (0.6.3 or later)
Runtime (OS2-EMX):
- OS/2 Warp V3 or later
- i486 or above CPU
- TCP/IP for OS/2
- EMX runtime (0.9d fix 04)
(Note zlib 1.2.7 has linked statically with runtime DLLs.)
Development Kit:
- (OS2-KNIX) gcc 3.3.5 or later
- (OS2-EMX) gcc 2.8.1
- zlib (1.2.8)
Quick and Dirty Installation (OS2-KNIX)
---------------------------------------
Runtime:
1. unzip runtime zip into some directory.
2. add '(the directory)\bin' to PATH
3. add '(the directory)\dll' to LIBPATH
4. set the environment variable OPENSSL_CONF to point 'ssl/openssl.cnf'
set OPENSSL_CONF=(the directory)\ssl\openssl.cnf
(I have no idea about which is the best directory for end-users (non-developer)
to install runtime.
some ideas... e.g.
/usr/local (openssl default configuration)
/usr (commonly unix style)
/etc (some unix style)
/MPTN/ETC (some unix style, a la OS/2)
/extras (Paul Smedley's bldenv)
/openssl (unique directory for openssl)
x:\OS2 (installed as OS2/eCS `system' components)
It is supposed the development kit will be installed into the
directory /extras, bacause this package is configured with '--prefix=/extras'.
)
Quick and Dirty Installation (OS2-EMX)
---------------------------------------
Runtime:
- copy os2_dll\openssl.exe into \emx\bin.
- copy os2_dll\*.dll into \emx\dll.
Development kit:
- copy os2_include\* into \emx\include.
- copy os2_dll\*.a and os2_dll\*.lib into \emx\lib.
How to build runtime DLLs and libraries
---------------------------------------
Prerequisites:
- EMX runtime and development kits
- perl
- grep
- sed
- Unix style shell sh.exe
- GNU make
- Unix style utilities: cp, mv, rm (and more, maybe)
- NetLabs gcc 3.3.5 or later (OS2-KNIX)
- Unix style patch to apply *.diff
Configuration and Make (OS2-EMX):
on OS/2 command prompt:
> os2\OS2-EMX default
> make -f OS2-EMX-DLL.mak
Configuration and Make (OS2-KNIX):
on OS/2 command prompt:
> os2\OS2-KNIX default
> make -f OS2-KNIX-DLL.mak
(and see INSTALL.OS2 in official OpenSSL package.) |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8za-os2knix-20140606-dev.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8za-os2knix-20140606-dev.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0m (toolkit, 6/6/2014) |
Readme/What's new |
2014-06-06
- openssl 1.0.0m |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0m-os2knix-20140606-dev.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0m-os2knix-20140606-dev.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8za (runtime, 6/6/2014) |
Readme/What's new |
OpenSSL 0.9.8za experimental port
for genuine EMX (OS2-EMX)
and klibc 0.6.x (OS2-KNIX).
System Requirement
------------------
Runtime (OS2-KNIX):
- OS/2 Warp V4 or later
- Pentium or above CPU
- 32 bit TCP/IP for OS/2 (TCPIP32)
- kLIBC 0.6.x (0.6.3 or later)
Runtime (OS2-EMX):
- OS/2 Warp V3 or later
- i486 or above CPU
- TCP/IP for OS/2
- EMX runtime (0.9d fix 04)
(Note zlib 1.2.7 has linked statically with runtime DLLs.)
Development Kit:
- (OS2-KNIX) gcc 3.3.5 or later
- (OS2-EMX) gcc 2.8.1
- zlib (1.2.8)
Quick and Dirty Installation (OS2-KNIX)
---------------------------------------
Runtime:
1. unzip runtime zip into some directory.
2. add '(the directory)\bin' to PATH
3. add '(the directory)\dll' to LIBPATH
4. set the environment variable OPENSSL_CONF to point 'ssl/openssl.cnf'
set OPENSSL_CONF=(the directory)\ssl\openssl.cnf
(I have no idea about which is the best directory for end-users (non-developer)
to install runtime.
some ideas... e.g.
/usr/local (openssl default configuration)
/usr (commonly unix style)
/etc (some unix style)
/MPTN/ETC (some unix style, a la OS/2)
/extras (Paul Smedley's bldenv)
/openssl (unique directory for openssl)
x:\OS2 (installed as OS2/eCS `system' components)
It is supposed the development kit will be installed into the
directory /extras, bacause this package is configured with '--prefix=/extras'.
)
Quick and Dirty Installation (OS2-EMX)
---------------------------------------
Runtime:
- copy os2_dll\openssl.exe into \emx\bin.
- copy os2_dll\*.dll into \emx\dll.
Development kit:
- copy os2_include\* into \emx\include.
- copy os2_dll\*.a and os2_dll\*.lib into \emx\lib.
How to build runtime DLLs and libraries
---------------------------------------
Prerequisites:
- EMX runtime and development kits
- perl
- grep
- sed
- Unix style shell sh.exe
- GNU make
- Unix style utilities: cp, mv, rm (and more, maybe)
- NetLabs gcc 3.3.5 or later (OS2-KNIX)
- Unix style patch to apply *.diff
Configuration and Make (OS2-EMX):
on OS/2 command prompt:
> os2\OS2-EMX default
> make -f OS2-EMX-DLL.mak
Configuration and Make (OS2-KNIX):
on OS/2 command prompt:
> os2\OS2-KNIX default
> make -f OS2-KNIX-DLL.mak
(and see INSTALL.OS2 in official OpenSSL package.) |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8za-os2knix-20140606-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8za-os2knix-20140606-runtime.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0m (runtime, 6/6/2014) |
Readme/What's new |
2014-06-06
- openssl 1.0.0m |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0m-os2knix-20140606-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0m-os2knix-20140606-runtime.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0l (fix 2, 14/5/2014, lpproj) |
Readme/What's new |
2014-05-14
- security fix: CVE-2014-0198 |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0l-fix2-os2emx-20140514.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0l-fix2-os2emx-20140514.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0l (toolkit, fix 2, 14/5/2014, lpproj) |
Readme/What's new |
2014-05-14
- security fix: CVE-2014-0198 |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0l-fix2-os2knix-20140514-dev.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0l-fix2-os2knix-20140514-dev.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0l (runtime, fix 2, 14/5/2014, lpproj) |
Readme/What's new |
2014-05-14
- security fix: CVE-2014-0198 |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0l-fix2-os2knix-20140514-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0l-fix2-os2knix-20140514-runtime.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0l (fix 1, 11/5/2014, lpproj) |
Readme/What's new |
OpenSSL 1.0.0l *experimental* port for OS/2 (EMX, kLIBC 0.6.x)
Important change(s) from 0.9.8 (for OS/2):
- different DLL module name. (I think that v1.0.0 has not `complete-
upward-compatibility' with v0.9.8. Some functions are missing...)
Installation (OS2-KNIX):
1. unzip runtime-zip into some directory.
2. unzip dev-zip into the same directory (if you need development toolkit).
3. add '(the directory)\bin' to PATH
4. add '(the directory)\dll' to LIBPATH
5. set the environment variable OPENSSL_CONF to point 'ssl/openssl.cnf'
set OPENSSL_CONF=(the directory)\ssl\openssl.cnf
(I have no idea about which is the best directory for end-users (non-developer)
to install runtime.
some ideas... e.g.
/usr/local (openssl default configuration)
/usr (commonly unix style)
/etc (some unix style)
/MPTN/ETC (some unix style, a la OS/2)
/extras (Paul Smedley's bldenv)
/openssl (unique directory for openssl)
x:\OS2 (installed as OS2/eCS `system' components)
It is supposed the development kit will be installed into the
directory /extras, bacause this package is configured with '--prefix=/extras'.)
Installation (OS2-EMX)
1. just unzip os2emx-package into the directory \emx.
How to build (OS2-KNIX):
1. apply the patch.
2. os2\OS2-KNIX.cmd default
3. make -f os2/OS2-KNIX-DLL.mak
How to build (OS2-EMX):
1. apply the patch.
2. os2\OS2-EMX.cmd default
3. make -f os2/OS2-EMX-DLL.mak
note: You should need updated bintuils (as.exe).
History:
2010-04-07
- configured for generic `gcc' build, without assembly codes and
experimental features.
2010-04-09
- OS2-EMX, OS2-KNIX build (using assembly codes)
2010-06-03
- version 1.0.0a
2010-06-30
- crypto/rand/rand_os2.c: fix thread-unsafed RAND_pool()
2010-10-04
- crypto/rand/rand_os2.c:
more fix RAND_pool() for more-than-2 CPUs (replacing DosPerfSysCall
with libc's random)
(I hope someone will write proper CSPRNG like /dev/random on modern
Unix-like systems for OS2/eCS...)
2010-10-13
- e_os.h: use syslog (BIO_s_log) on knix
2010-11-17
- openssl 1.0.0b
2010-12-03
- openssl 1.0.0c
2011-02-09
- openssl 1.0.0d
- fixed: import libraries' name
(crypto.a -> libcrypto.a, ssl.a -> libssl.a)
2011-09-10
- openssl 1.0.0e
- workaround for parallel build
(make -f OS2-KNIX-DLL.mak mkdirs && make -f OS2-KNIX-DLL.mak -j4)
2012-01-07
- openssl 1.0.0f
- with zlib 1.2.5
2012-01-21
- openssl 1.0.0g
2012-03-13
- openssl 1.0.0h
2012-04-20
- openssl 1.0.0i
2012-05-11
- openssl 1.0.0j
- default configuration
CFLAGS: -march=pentium -mtune=generic (OS2KNIX)
LDFLAGS: -Zhigh-mem (OS2KNIX)
2013-02-07
- openssl 1.0.0k
- with zlib 1.2.7
- applied http://svn.netlabs.org/ports/changeset/578
2014-01-08
- openssl 1.0.0l
- with zlib 1.2.8
2014-05-11
- security fixes: CVE-2010-5298 and CVE-2014-0076 |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0l-fix1-os2emx-20140511.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0l-fix1-os2emx-20140511.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0l (toolkit, fix 1, 11/5/2014, lpproj) |
Readme/What's new |
2014-05-11
- security fixes: CVE-2010-5298 and CVE-2014-0076 |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0l-fix1-os2knix-20140511-dev.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0l-fix1-os2knix-20140511-dev.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0l (runtime, fix 1, 11/5/2014, lpproj) |
Readme/What's new |
2014-05-11
- security fixes: CVE-2010-5298 and CVE-2014-0076 |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0l-fix1-os2knix-20140511-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0l-fix1-os2knix-20140511-runtime.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0k (7/2/2013) |
Readme/What's new |
OpenSSL 1.0.0k *experimental* port for OS/2 (EMX, kLIBC 0.6.x)
Important change(s) from 0.9.8 (for OS/2):
- different DLL module name. (I think that v1.0.0 has not `complete-
upward-compatibility' with v0.9.8. Some functions are missing...)
Installation (OS2-KNIX):
1. unzip runtime-zip into some directory.
2. unzip dev-zip into the same directory (if you need development toolkit).
3. add '(the directory)\bin' to PATH
4. add '(the directory)\dll' to LIBPATH
5. set the environment variable OPENSSL_CONF to point 'ssl/openssl.cnf'
set OPENSSL_CONF=(the directory)\ssl\openssl.cnf
(I have no idea about which is the best directory for end-users (non-developer)
to install runtime.
some ideas... e.g.
/usr/local (openssl default configuration)
/usr (commonly unix style)
/etc (some unix style)
/MPTN/ETC (some unix style, a la OS/2)
/extras (Paul Smedley's bldenv)
/openssl (unique directory for openssl)
x:\OS2 (installed as OS2/eCS `system' components)
It is supposed the development kit will be installed into the
directory /extras, bacause this package is configured with '--prefix=/extras'.)
Installation (OS2-EMX)
1. just unzip os2emx-package into the directory \emx.
How to build (OS2-KNIX):
1. apply the patch.
2. os2\OS2-KNIX.cmd default
3. make -f os2/OS2-KNIX-DLL.mak
How to build (OS2-EMX):
1. apply the patch.
2. os2\OS2-EMX.cmd default
3. make -f os2/OS2-EMX-DLL.mak
note: You should need updated bintuils (as.exe).
History:
2010-04-07
- configured for generic `gcc' build, without assembly codes and
experimental features.
2010-04-09
- OS2-EMX, OS2-KNIX build (using assembly codes)
2010-06-03
- version 1.0.0a
2010-06-30
- crypto/rand/rand_os2.c: fix thread-unsafed RAND_pool()
2010-10-04
- crypto/rand/rand_os2.c:
more fix RAND_pool() for more-than-2 CPUs (replacing DosPerfSysCall
with libc's random)
(I hope someone will write proper CSPRNG like /dev/random on modern
Unix-like systems for OS2/eCS...)
2010-10-13
- e_os.h: use syslog (BIO_s_log) on knix
2010-11-17
- openssl 1.0.0b
2010-12-03
- openssl 1.0.0c
2011-02-09
- openssl 1.0.0d
- fixed: import libraries' name
(crypto.a -> libcrypto.a, ssl.a -> libssl.a)
2011-09-10
- openssl 1.0.0e
- workaround for parallel build
(make -f OS2-KNIX-DLL.mak mkdirs && make -f OS2-KNIX-DLL.mak -j4)
2012-01-07
- openssl 1.0.0f
- with zlib 1.2.5
2012-01-21
- openssl 1.0.0g
2012-03-13
- openssl 1.0.0h
2012-04-20
- openssl 1.0.0i
2012-05-11
- openssl 1.0.0j
- default configuration
CFLAGS: -march=pentium -mtune=generic (OS2KNIX)
LDFLAGS: -Zhigh-mem (OS2KNIX)
2013-02-07
- openssl 1.0.0k
- with zlib 1.2.7
- applied http://svn.netlabs.org/ports/changeset/578 |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0k-os2emx-20130207.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0k-os2emx-20130207.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0k (toolkit, 7/2/2013) |
Readme/What's new |
OpenSSL 1.0.0k *experimental* port for OS/2 (EMX, kLIBC 0.6.x)
Important change(s) from 0.9.8 (for OS/2):
- different DLL module name. (I think that v1.0.0 has not `complete-
upward-compatibility' with v0.9.8. Some functions are missing...)
Installation (OS2-KNIX):
1. unzip runtime-zip into some directory.
2. unzip dev-zip into the same directory (if you need development toolkit).
3. add '(the directory)\bin' to PATH
4. add '(the directory)\dll' to LIBPATH
5. set the environment variable OPENSSL_CONF to point 'ssl/openssl.cnf'
set OPENSSL_CONF=(the directory)\ssl\openssl.cnf
(I have no idea about which is the best directory for end-users (non-developer)
to install runtime.
some ideas... e.g.
/usr/local (openssl default configuration)
/usr (commonly unix style)
/etc (some unix style)
/MPTN/ETC (some unix style, a la OS/2)
/extras (Paul Smedley's bldenv)
/openssl (unique directory for openssl)
x:\OS2 (installed as OS2/eCS `system' components)
It is supposed the development kit will be installed into the
directory /extras, bacause this package is configured with '--prefix=/extras'.)
Installation (OS2-EMX)
1. just unzip os2emx-package into the directory \emx.
How to build (OS2-KNIX):
1. apply the patch.
2. os2\OS2-KNIX.cmd default
3. make -f os2/OS2-KNIX-DLL.mak
How to build (OS2-EMX):
1. apply the patch.
2. os2\OS2-EMX.cmd default
3. make -f os2/OS2-EMX-DLL.mak
note: You should need updated bintuils (as.exe).
History:
2010-04-07
- configured for generic `gcc' build, without assembly codes and
experimental features.
2010-04-09
- OS2-EMX, OS2-KNIX build (using assembly codes)
2010-06-03
- version 1.0.0a
2010-06-30
- crypto/rand/rand_os2.c: fix thread-unsafed RAND_pool()
2010-10-04
- crypto/rand/rand_os2.c:
more fix RAND_pool() for more-than-2 CPUs (replacing DosPerfSysCall
with libc's random)
(I hope someone will write proper CSPRNG like /dev/random on modern
Unix-like systems for OS2/eCS...)
2010-10-13
- e_os.h: use syslog (BIO_s_log) on knix
2010-11-17
- openssl 1.0.0b
2010-12-03
- openssl 1.0.0c
2011-02-09
- openssl 1.0.0d
- fixed: import libraries' name
(crypto.a -> libcrypto.a, ssl.a -> libssl.a)
2011-09-10
- openssl 1.0.0e
- workaround for parallel build
(make -f OS2-KNIX-DLL.mak mkdirs && make -f OS2-KNIX-DLL.mak -j4)
2012-01-07
- openssl 1.0.0f
- with zlib 1.2.5
2012-01-21
- openssl 1.0.0g
2012-03-13
- openssl 1.0.0h
2012-04-20
- openssl 1.0.0i
2012-05-11
- openssl 1.0.0j
- default configuration
CFLAGS: -march=pentium -mtune=generic (OS2KNIX)
LDFLAGS: -Zhigh-mem (OS2KNIX)
2013-02-07
- openssl 1.0.0k
- with zlib 1.2.7
- applied http://svn.netlabs.org/ports/changeset/578 |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0k-os2knix-20130207-dev.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0k-os2knix-20130207-dev.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0k (runtime, 7/2/2013) |
Readme/What's new |
2013-02-07
- openssl 1.0.0k
- with zlib 1.2.7
- applied http://svn.netlabs.org/ports/changeset/578 |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0k-os2knix-20130207-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0k-os2knix-20130207-runtime.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8y (emx, 6/2/2013) |
Readme/What's new |
OpenSSL 0.9.8y experimental port
for genuine EMX (OS2-EMX)
and klibc 0.6.x (OS2-KNIX).
System Requirement
------------------
Runtime (OS2-KNIX):
- OS/2 Warp V4 or later
- Pentium or above CPU
- 32 bit TCP/IP for OS/2 (TCPIP32)
- kLIBC 0.6.x (0.6.3 or later)
Runtime (OS2-EMX):
- OS/2 Warp V3 or later
- i486 or above CPU
- TCP/IP for OS/2
- EMX runtime (0.9d fix 04)
(Note zlib 1.2.7 has linked statically with runtime DLLs.)
Development Kit:
- (OS2-KNIX) gcc 3.3.5 or later
- (OS2-EMX) gcc 2.8.1
- zlib (1.2.7)
Quick and Dirty Installation (OS2-KNIX)
---------------------------------------
Runtime:
1. unzip runtime zip into some directory.
2. add '(the directory)\bin' to PATH
3. add '(the directory)\dll' to LIBPATH
4. set the environment variable OPENSSL_CONF to point 'ssl/openssl.cnf'
set OPENSSL_CONF=(the directory)\ssl\openssl.cnf
(I have no idea about which is the best directory for end-users (non-developer)
to install runtime.
some ideas... e.g.
/usr/local (openssl default configuration)
/usr (commonly unix style)
/etc (some unix style)
/MPTN/ETC (some unix style, a la OS/2)
/extras (Paul Smedley's bldenv)
/openssl (unique directory for openssl)
x:\OS2 (installed as OS2/eCS `system' components)
It is supposed the development kit will be installed into the
directory /extras, bacause this package is configured with '--prefix=/extras'.
)
Quick and Dirty Installation (OS2-EMX)
---------------------------------------
Runtime:
- copy os2_dll\openssl.exe into \emx\bin.
- copy os2_dll\*.dll into \emx\dll.
Development kit:
- copy os2_include\* into \emx\include.
- copy os2_dll\*.a and os2_dll\*.lib into \emx\lib.
How to build runtime DLLs and libraries
---------------------------------------
Prerequisites:
- EMX runtime and development kits
- perl
- grep
- sed
- Unix style shell sh.exe
- GNU make
- Unix style utilities: cp, mv, rm (and more, maybe)
- NetLabs gcc 3.3.5 or later (OS2-KNIX)
- Unix style patch to apply *.diff
Configuration and Make (OS2-EMX):
on OS/2 command prompt:
> os2\OS2-EMX default
> make -f OS2-EMX-DLL.mak
Configuration and Make (OS2-KNIX):
on OS/2 command prompt:
> os2\OS2-KNIX default
> make -f OS2-KNIX-DLL.mak
(and see INSTALL.OS2 in official OpenSSL package.) |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8y-os2emx-20130206.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8y-os2emx-20130206.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8y (toolkit, 6/2/2013) |
Readme/What's new |
OpenSSL 0.9.8y experimental port
for genuine EMX (OS2-EMX)
and klibc 0.6.x (OS2-KNIX).
System Requirement
------------------
Runtime (OS2-KNIX):
- OS/2 Warp V4 or later
- Pentium or above CPU
- 32 bit TCP/IP for OS/2 (TCPIP32)
- kLIBC 0.6.x (0.6.3 or later)
Runtime (OS2-EMX):
- OS/2 Warp V3 or later
- i486 or above CPU
- TCP/IP for OS/2
- EMX runtime (0.9d fix 04)
(Note zlib 1.2.7 has linked statically with runtime DLLs.)
Development Kit:
- (OS2-KNIX) gcc 3.3.5 or later
- (OS2-EMX) gcc 2.8.1
- zlib (1.2.7)
Quick and Dirty Installation (OS2-KNIX)
---------------------------------------
Runtime:
1. unzip runtime zip into some directory.
2. add '(the directory)\bin' to PATH
3. add '(the directory)\dll' to LIBPATH
4. set the environment variable OPENSSL_CONF to point 'ssl/openssl.cnf'
set OPENSSL_CONF=(the directory)\ssl\openssl.cnf
(I have no idea about which is the best directory for end-users (non-developer)
to install runtime.
some ideas... e.g.
/usr/local (openssl default configuration)
/usr (commonly unix style)
/etc (some unix style)
/MPTN/ETC (some unix style, a la OS/2)
/extras (Paul Smedley's bldenv)
/openssl (unique directory for openssl)
x:\OS2 (installed as OS2/eCS `system' components)
It is supposed the development kit will be installed into the
directory /extras, bacause this package is configured with '--prefix=/extras'.
)
Quick and Dirty Installation (OS2-EMX)
---------------------------------------
Runtime:
- copy os2_dll\openssl.exe into \emx\bin.
- copy os2_dll\*.dll into \emx\dll.
Development kit:
- copy os2_include\* into \emx\include.
- copy os2_dll\*.a and os2_dll\*.lib into \emx\lib.
How to build runtime DLLs and libraries
---------------------------------------
Prerequisites:
- EMX runtime and development kits
- perl
- grep
- sed
- Unix style shell sh.exe
- GNU make
- Unix style utilities: cp, mv, rm (and more, maybe)
- NetLabs gcc 3.3.5 or later (OS2-KNIX)
- Unix style patch to apply *.diff
Configuration and Make (OS2-EMX):
on OS/2 command prompt:
> os2\OS2-EMX default
> make -f OS2-EMX-DLL.mak
Configuration and Make (OS2-KNIX):
on OS/2 command prompt:
> os2\OS2-KNIX default
> make -f OS2-KNIX-DLL.mak
(and see INSTALL.OS2 in official OpenSSL package.) |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8y-os2knix-20130206-dev.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8y-os2knix-20130206-dev.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8y (runtime, 6/2/2013) |
Readme/What's new |
OpenSSL 0.9.8y experimental port
for genuine EMX (OS2-EMX)
and klibc 0.6.x (OS2-KNIX).
System Requirement
------------------
Runtime (OS2-KNIX):
- OS/2 Warp V4 or later
- Pentium or above CPU
- 32 bit TCP/IP for OS/2 (TCPIP32)
- kLIBC 0.6.x (0.6.3 or later)
Runtime (OS2-EMX):
- OS/2 Warp V3 or later
- i486 or above CPU
- TCP/IP for OS/2
- EMX runtime (0.9d fix 04)
(Note zlib 1.2.7 has linked statically with runtime DLLs.)
Development Kit:
- (OS2-KNIX) gcc 3.3.5 or later
- (OS2-EMX) gcc 2.8.1
- zlib (1.2.7)
Quick and Dirty Installation (OS2-KNIX)
---------------------------------------
Runtime:
1. unzip runtime zip into some directory.
2. add '(the directory)\bin' to PATH
3. add '(the directory)\dll' to LIBPATH
4. set the environment variable OPENSSL_CONF to point 'ssl/openssl.cnf'
set OPENSSL_CONF=(the directory)\ssl\openssl.cnf
(I have no idea about which is the best directory for end-users (non-developer)
to install runtime.
some ideas... e.g.
/usr/local (openssl default configuration)
/usr (commonly unix style)
/etc (some unix style)
/MPTN/ETC (some unix style, a la OS/2)
/extras (Paul Smedley's bldenv)
/openssl (unique directory for openssl)
x:\OS2 (installed as OS2/eCS `system' components)
It is supposed the development kit will be installed into the
directory /extras, bacause this package is configured with '--prefix=/extras'.
)
Quick and Dirty Installation (OS2-EMX)
---------------------------------------
Runtime:
- copy os2_dll\openssl.exe into \emx\bin.
- copy os2_dll\*.dll into \emx\dll.
Development kit:
- copy os2_include\* into \emx\include.
- copy os2_dll\*.a and os2_dll\*.lib into \emx\lib.
How to build runtime DLLs and libraries
---------------------------------------
Prerequisites:
- EMX runtime and development kits
- perl
- grep
- sed
- Unix style shell sh.exe
- GNU make
- Unix style utilities: cp, mv, rm (and more, maybe)
- NetLabs gcc 3.3.5 or later (OS2-KNIX)
- Unix style patch to apply *.diff
Configuration and Make (OS2-EMX):
on OS/2 command prompt:
> os2\OS2-EMX default
> make -f OS2-EMX-DLL.mak
Configuration and Make (OS2-KNIX):
on OS/2 command prompt:
> os2\OS2-KNIX default
> make -f OS2-KNIX-DLL.mak
(and see INSTALL.OS2 in official OpenSSL package.) |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8y-os2knix-20130206-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8y-os2knix-20130206-runtime.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0e (runtime, 10/9/2011) |
Readme/What's new |
History:
2010-04-07
- configured for generic `gcc' build, without assembly codes and
experimental features.
2010-04-09
- OS2-EMX, OS2-KNIX build (using assembly codes)
2010-06-03
- version 1.0.0a
2010-06-30
- crypto/rand/rand_os2.c: fix thread-unsafed RAND_pool()
2010-10-04
- crypto/rand/rand_os2.c:
more fix RAND_pool() for more-than-2 CPUs (replacing DosPerfSysCall
with libc's random)
(I hope someone will write proper CSPRNG like /dev/random on modern
Unix-like systems for OS2/eCS...)
2010-10-13
- e_os.h: use syslog (BIO_s_log) on knix
2010-11-17
- openssl 1.0.0b
2010-12-03
- openssl 1.0.0c
2011-02-09
- openssl 1.0.0d
- fixed: import libraries' name
(crypto.a -> libcrypto.a, ssl.a -> libssl.a)
2011-09-10
- openssl 1.0.0e
- workaround for parallel build
(make -f OS2-KNIX-DLL.mak mkdirs && make -f OS2-KNIX-DLL.mak -j4) |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0e-os2knix-20110910-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0e-os2knix-20110910-runtime.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0a (toolkit, 3/6/2010, T. Ebisawa) |
Readme/What's new |
OpenSSL 1.0.0a *experimental* port for OS/2 (EMX, kLIBC)
Important change(s) from 0.9.8 (for OS/2):
- different DLL module name. (I think that v1.0.0 has not `complete-
upward-compatibility' with v0.9.8. Some functions are missing...)
Installation (OS2-KNIX):
1. unzip runtime-zip into some directory.
2. unzip dev-zip into the same directory (if you need development toolkit).
3. add '(the directory)\bin' to PATH
4. add '(the directory)\dll' to LIBPATH
5. set the environment variable OPENSSL_CONF to point 'ssl/openssl.cnf'
set OPENSSL_CONF=(the directory)\ssl\openssl.cnf
(I have no idea about which is the best directory for end-users (non-developer)
to install runtime.
some ideas... e.g.
/usr/local (openssl default configuration)
/usr (commonly unix style)
/etc (some unix style)
/MPTN/ETC (some unix style, a la OS/2)
/extras (Paul Smedley's bldenv)
/openssl (unique directory for openssl)
x:\OS2 (installed as OS2/eCS `system' components)
It is supposed the development kit will be installed into the
directory /extras, bacause this package is configured with '--prefix=/extras'.)
Installation (OS2-EMX)
1. just unzip os2emx-package into the directory \emx.
How to build (OS2-KNIX):
1. apply the patch.
2. os2\OS2-KNIX.cmd default
3. make -f os2/OS2-KNIX-DLL.mak
How to build (OS2-EMX):
1. apply the patch.
2. os2\OS2-EMX.cmd default
3. make -f os2/OS2-EMX-DLL.mak
note: You should need updated bintuils (as.exe).
History:
2010-04-07
- configured for generic `gcc' build, without assembly codes and
experimental features.
2010-04-09
- OS2-EMX, OS2-KNIX build (with assmbly codes)
2010-06-03
- version 1.0.0a |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0a-os2knix-20100603-dev.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0a-os2knix-20100603-dev.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0a (runtime, 3/6/2010, T. Ebisawa) |
Readme/What's new |
History:
2010-04-07
- configured for generic `gcc' build, without assembly codes and
experimental features.
2010-04-09
- OS2-EMX, OS2-KNIX build (with assmbly codes)
2010-06-03
- version 1.0.0a |
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0a-os2knix-20100603-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0a-os2knix-20100603-runtime.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8o (toolkit, 2/6/2010, T. Ebisawa) |
Readme/What's new |
OpenSSL 0.9.8o experimental port
for genuine EMX (OS2-EMX)
and klibc 0.6.x (OS2-KNIX).
System Requirement
------------------
Runtime (OS2-KNIX):
- OS/2 Warp V4 or later
- Pentium or above CPU
- 32 bit TCP/IP for OS/2 (TCPIP32)
- kLIBC 0.6.3
Runtime (OS2-EMX):
- OS/2 Warp V3 or later
- i486 or above CPU
- TCP/IP for OS/2
- EMX runtime (0.9d fix 04)
(Note zlib 1.2.3 has linked statically with runtime DLLs.)
Development Kit:
- (OS2-KNIX) gcc 3.3.5 or later
- (OS2-EMX) gcc 2.8.1
- zlib (1.2.3)
System Recommendation
---------------------
- perl (5.10 or later)
Quick and Dirty Installation (OS2-KNIX)
---------------------------------------
Runtime:
1. unzip runtime zip into some directory.
2. add '(the directory)\bin' to PATH
3. add '(the directory)\dll' to LIBPATH
4. set the environment variable OPENSSL_CONF to point 'ssl/openssl.cnf'
set OPENSSL_CONF=(the directory)\ssl\openssl.cnf
(I have no idea about which is the best directory for end-users (non-developer)
to install runtime.
some ideas... e.g.
/usr/local (openssl default configuration)
/usr (commonly unix style)
/etc (some unix style)
/MPTN/ETC (some unix style, a la OS/2)
/extras (Paul Smedley's bldenv)
/openssl (unique directory for openssl)
x:\OS2 (installed as OS2/eCS `system' components)
It is supposed the development kit will be installed into the
directory /extras, bacause this package is configured with '--prefix=/extras'.
)
Quick and Dirty Installation (OS2-EMX)
---------------------------------------
Runtime:
- copy os2_dll/openssl.exe into \emx\bin.
- copy os2_dll/*.dll into \emx\dll.
Development kit:
- copy os2_include/* into \emx\include.
- copy os2_dll/*.a and os2_dll/*.lib into \emx\lib.
How to build runtime DLLs and libraries
---------------------------------------
Prerequisites:
- EMX runtime and development kits
- perl
- grep
- sed
- Unix style shell sh.exe
- GNU make
- Unix style utilities: cp, mv, rm (and more, maybe)
- NetLabs gcc 3.3.5 or later (OS2-KNIX)
- Unix style patch to apply *.diff
Configuration and Make (OS2-EMX):
on OS/2 command prompt:
> os2\OS2-EMX default
> make -f OS2-EMX-DLL.mak
Configuration and Make (OS2-KNIX):
on OS/2 command prompt:
> os2\OS2-KNIX default
> make -f OS2-KNIX-DLL.mak
(and see INSTALL.OS2 in official OpenSSL package.) |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8o-os2knix-20100602-dev.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8o-os2knix-20100602-dev.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8o (runtime, 2/6/2010, T. Ebisawa) |
Readme/What's new |
OpenSSL 0.9.8o experimental port
for genuine EMX (OS2-EMX)
and klibc 0.6.x (OS2-KNIX).
System Requirement
------------------
Runtime (OS2-KNIX):
- OS/2 Warp V4 or later
- Pentium or above CPU
- 32 bit TCP/IP for OS/2 (TCPIP32)
- kLIBC 0.6.3
Runtime (OS2-EMX):
- OS/2 Warp V3 or later
- i486 or above CPU
- TCP/IP for OS/2
- EMX runtime (0.9d fix 04)
(Note zlib 1.2.3 has linked statically with runtime DLLs.)
Development Kit:
- (OS2-KNIX) gcc 3.3.5 or later
- (OS2-EMX) gcc 2.8.1
- zlib (1.2.3)
System Recommendation
---------------------
- perl (5.10 or later)
Quick and Dirty Installation (OS2-KNIX)
---------------------------------------
Runtime:
1. unzip runtime zip into some directory.
2. add '(the directory)\bin' to PATH
3. add '(the directory)\dll' to LIBPATH
4. set the environment variable OPENSSL_CONF to point 'ssl/openssl.cnf'
set OPENSSL_CONF=(the directory)\ssl\openssl.cnf
(I have no idea about which is the best directory for end-users (non-developer)
to install runtime.
some ideas... e.g.
/usr/local (openssl default configuration)
/usr (commonly unix style)
/etc (some unix style)
/MPTN/ETC (some unix style, a la OS/2)
/extras (Paul Smedley's bldenv)
/openssl (unique directory for openssl)
x:\OS2 (installed as OS2/eCS `system' components)
It is supposed the development kit will be installed into the
directory /extras, bacause this package is configured with '--prefix=/extras'.
)
Quick and Dirty Installation (OS2-EMX)
---------------------------------------
Runtime:
- copy os2_dll/openssl.exe into \emx\bin.
- copy os2_dll/*.dll into \emx\dll.
Development kit:
- copy os2_include/* into \emx\include.
- copy os2_dll/*.a and os2_dll/*.lib into \emx\lib.
How to build runtime DLLs and libraries
---------------------------------------
Prerequisites:
- EMX runtime and development kits
- perl
- grep
- sed
- Unix style shell sh.exe
- GNU make
- Unix style utilities: cp, mv, rm (and more, maybe)
- NetLabs gcc 3.3.5 or later (OS2-KNIX)
- Unix style patch to apply *.diff
Configuration and Make (OS2-EMX):
on OS/2 command prompt:
> os2\OS2-EMX default
> make -f OS2-EMX-DLL.mak
Configuration and Make (OS2-KNIX):
on OS/2 command prompt:
> os2\OS2-KNIX default
> make -f OS2-KNIX-DLL.mak
(and see INSTALL.OS2 in official OpenSSL package.) |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8o-os2knix-20100602-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8o-os2knix-20100602-runtime.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8n (toolkit, 27/3/2010, T. Ebisawa) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8m and 0.9.8n [24 Mar 2010]
*) When rejecting SSL/TLS records due to an incorrect version number, never
update s->server with a new major version number. As of
- OpenSSL 0.9.8m if 'short' is a 16-bit type,
- OpenSSL 0.9.8f if 'short' is longer than 16 bits,
the previous behavior could result in a read attempt at NULL when
receiving specific incorrect SSL/TLS records once record payload
protection is active. (CVE-2010-0740)
[Bodo Moeller, Adam Langley <agl@chromium.org>]
*) Fix for CVE-2010-0433 where some kerberos enabled versions of OpenSSL
could be crashed if the relevant tables were not present (e.g. chrooted).
[Tomas Hoger <thoger@redhat.com>] |
 hobbes.nmsu.edu/download/pub/os2/util/encrypt/openssl-0.9.8n-os2knix-20100325-dev.zip hobbes.nmsu.edu/download/pub/os2/util/encrypt/openssl-0.9.8n-os2knix-20100325-dev.zip |
|
|
OpenSSL v. 0.9.8n (runtime, 27/3/2010, T. Ebisawa) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8m and 0.9.8n [24 Mar 2010]
*) When rejecting SSL/TLS records due to an incorrect version number, never
update s->server with a new major version number. As of
- OpenSSL 0.9.8m if 'short' is a 16-bit type,
- OpenSSL 0.9.8f if 'short' is longer than 16 bits,
the previous behavior could result in a read attempt at NULL when
receiving specific incorrect SSL/TLS records once record payload
protection is active. (CVE-2010-0740)
[Bodo Moeller, Adam Langley <agl@chromium.org>]
*) Fix for CVE-2010-0433 where some kerberos enabled versions of OpenSSL
could be crashed if the relevant tables were not present (e.g. chrooted).
[Tomas Hoger <thoger@redhat.com>] |
 hobbes.nmsu.edu/download/pub/os2/util/encrypt/openssl-0.9.8n-os2knix-20100325-runtime.zip hobbes.nmsu.edu/download/pub/os2/util/encrypt/openssl-0.9.8n-os2knix-20100325-runtime.zip |
|
|
OpenSSL v. 0.9.8m (28/2/2010) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8l and 0.9.8m [25 Feb 2010]
*) Always check bn_wexpend() return values for failure. (CVE-2009-3245)
[Martin Olsson, Neel Mehta]
*) Fix X509_STORE locking: Every 'objs' access requires a lock (to
accommodate for stack sorting, always a write lock!).
[Bodo Moeller]
*) On some versions of WIN32 Heap32Next is very slow. This can cause
excessive delays in the RAND_poll(): over a minute. As a workaround
include a time check in the inner Heap32Next loop too.
[Steve Henson]
*) The code that handled flushing of data in SSL/TLS originally used the
BIO_CTRL_INFO ctrl to see if any data was pending first. This caused
the problem outlined in PR#1949. The fix suggested there however can
trigger problems with buggy BIO_CTRL_WPENDING (e.g. some versions
of Apache). So instead simplify the code to flush unconditionally.
This should be fine since flushing with no data to flush is a no op.
[Steve Henson]
*) Handle TLS versions 2.0 and later properly and correctly use the
highest version of TLS/SSL supported. Although TLS >= 2.0 is some way
off ancient servers have a habit of sticking around for a while...
[Steve Henson]
*) Modify compression code so it frees up structures without using the
ex_data callbacks. This works around a problem where some applications
call CRYPTO_cleanup_all_ex_data() before application exit (e.g. when
restarting) then use compression (e.g. SSL with compression) later.
This results in significant per-connection memory leaks and
has caused some security issues including CVE-2008-1678 and
CVE-2009-4355.
[Steve Henson]
*) Constify crypto/cast (i.e., <openssl/cast.h>): a CAST_KEY doesn't
change when encrypting or decrypting.
[Bodo Moeller]
*) Add option SSL_OP_LEGACY_SERVER_CONNECT which will allow clients to
connect and renegotiate with servers which do not support RI.
Until RI is more widely deployed this option is enabled by default.
[Steve Henson]
*) Add "missing" ssl ctrls to clear options and mode.
[Steve Henson]
*) If client attempts to renegotiate and doesn't support RI respond with
a no_renegotiation alert as required by RFC5746. Some renegotiating
TLS clients will continue a connection gracefully when they receive
the alert. Unfortunately OpenSSL mishandled this alert and would hang
waiting for a server hello which it will never receive. Now we treat a
received no_renegotiation alert as a fatal error. This is because
applications requesting a renegotiation might well expect it to succeed
and would have no code in place to handle the server denying it so the
only safe thing to do is to terminate the connection.
[Steve Henson]
*) Add ctrl macro SSL_get_secure_renegotiation_support() which returns 1 if
peer supports secure renegotiation and 0 otherwise. Print out peer
renegotiation support in s_client/s_server.
[Steve Henson]
*) Replace the highly broken and deprecated SPKAC certification method with
the updated NID creation version. This should correctly handle UTF8.
[Steve Henson]
*) Implement RFC5746. Re-enable renegotiation but require the extension
as needed. Unfortunately, SSL3_FLAGS_ALLOW_UNSAFE_LEGACY_RENEGOTIATION
turns out to be a bad idea. It has been replaced by
SSL_OP_ALLOW_UNSAFE_LEGACY_RENEGOTIATION which can be set with
SSL_CTX_set_options(). This is really not recommended unless you
know what you are doing.
[Eric Rescorla <ekr@networkresonance.com>, Ben Laurie, Steve Henson]
*) Fixes to stateless session resumption handling. Use initial_ctx when
issuing and attempting to decrypt tickets in case it has changed during
servername handling. Use a non-zero length session ID when attempting
stateless session resumption: this makes it possible to determine if
a resumption has occurred immediately after receiving server hello
(several places in OpenSSL subtly assume this) instead of later in
the handshake.
[Steve Henson]
*) The functions ENGINE_ctrl(), OPENSSL_isservice(),
CMS_get1_RecipientRequest() and RAND_bytes() can return <=0 on error
fixes for a few places where the return code is not checked
correctly.
[Julia Lawall <julia@diku.dk>]
*) Add --strict-warnings option to Configure script to include devteam
warnings in other configurations.
[Steve Henson]
*) Add support for --libdir option and LIBDIR variable in makefiles. This
makes it possible to install openssl libraries in locations which
have names other than "lib", for example "/usr/lib64" which some
systems need.
[Steve Henson, based on patch from Jeremy Utley]
*) Don't allow the use of leading 0x80 in OIDs. This is a violation of
X690 8.9.12 and can produce some misleading textual output of OIDs.
[Steve Henson, reported by Dan Kaminsky]
*) Delete MD2 from algorithm tables. This follows the recommendation in
several standards that it is not used in new applications due to
several cryptographic weaknesses. For binary compatibility reasons
the MD2 API is still compiled in by default.
[Steve Henson]
*) Add compression id to {d2i,i2d}_SSL_SESSION so it is correctly saved
and restored.
[Steve Henson]
*) Rename uni2asc and asc2uni functions to OPENSSL_uni2asc and
OPENSSL_asc2uni conditionally on Netware platforms to avoid a name
clash.
[Guenter <lists@gknw.net>]
*) Fix the server certificate chain building code to use X509_verify_cert(),
it used to have an ad-hoc builder which was unable to cope with anything
other than a simple chain.
[David Woodhouse <dwmw2@infradead.org>, Steve Henson]
*) Don't check self signed certificate signatures in X509_verify_cert()
by default (a flag can override this): it just wastes time without
adding any security. As a useful side effect self signed root CAs
with non-FIPS digests are now usable in FIPS mode.
[Steve Henson]
*) In dtls1_process_out_of_seq_message() the check if the current message
is already buffered was missing. For every new message was memory
allocated, allowing an attacker to perform an denial of service attack
with sending out of seq handshake messages until there is no memory
left. Additionally every future messege was buffered, even if the
sequence number made no sense and would be part of another handshake.
So only messages with sequence numbers less than 10 in advance will be
buffered. (CVE-2009-1378)
[Robin Seggelmann, discovered by Daniel Mentz]
*) Records are buffered if they arrive with a future epoch to be
processed after finishing the corresponding handshake. There is
currently no limitation to this buffer allowing an attacker to perform
a DOS attack with sending records with future epochs until there is no
memory left. This patch adds the pqueue_size() function to detemine
the size of a buffer and limits the record buffer to 100 entries.
(CVE-2009-1377)
[Robin Seggelmann, discovered by Daniel Mentz]
*) Keep a copy of frag->msg_header.frag_len so it can be used after the
parent structure is freed. (CVE-2009-1379)
[Daniel Mentz]
*) Handle non-blocking I/O properly in SSL_shutdown() call.
[Darryl Miles <darryl-mailinglists@netbauds.net>]
*) Add 2.5.4.* OIDs
[Ilya O. <vrghost@gmail.com>] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8m-os2emx-20100228.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8m-os2emx-20100228.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8m (toolkit, 28/2/2010) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8l and 0.9.8m [25 Feb 2010]
*) Always check bn_wexpend() return values for failure. (CVE-2009-3245)
[Martin Olsson, Neel Mehta]
*) Fix X509_STORE locking: Every 'objs' access requires a lock (to
accommodate for stack sorting, always a write lock!).
[Bodo Moeller]
*) On some versions of WIN32 Heap32Next is very slow. This can cause
excessive delays in the RAND_poll(): over a minute. As a workaround
include a time check in the inner Heap32Next loop too.
[Steve Henson]
*) The code that handled flushing of data in SSL/TLS originally used the
BIO_CTRL_INFO ctrl to see if any data was pending first. This caused
the problem outlined in PR#1949. The fix suggested there however can
trigger problems with buggy BIO_CTRL_WPENDING (e.g. some versions
of Apache). So instead simplify the code to flush unconditionally.
This should be fine since flushing with no data to flush is a no op.
[Steve Henson]
*) Handle TLS versions 2.0 and later properly and correctly use the
highest version of TLS/SSL supported. Although TLS >= 2.0 is some way
off ancient servers have a habit of sticking around for a while...
[Steve Henson]
*) Modify compression code so it frees up structures without using the
ex_data callbacks. This works around a problem where some applications
call CRYPTO_cleanup_all_ex_data() before application exit (e.g. when
restarting) then use compression (e.g. SSL with compression) later.
This results in significant per-connection memory leaks and
has caused some security issues including CVE-2008-1678 and
CVE-2009-4355.
[Steve Henson]
*) Constify crypto/cast (i.e., <openssl/cast.h>): a CAST_KEY doesn't
change when encrypting or decrypting.
[Bodo Moeller]
*) Add option SSL_OP_LEGACY_SERVER_CONNECT which will allow clients to
connect and renegotiate with servers which do not support RI.
Until RI is more widely deployed this option is enabled by default.
[Steve Henson]
*) Add "missing" ssl ctrls to clear options and mode.
[Steve Henson]
*) If client attempts to renegotiate and doesn't support RI respond with
a no_renegotiation alert as required by RFC5746. Some renegotiating
TLS clients will continue a connection gracefully when they receive
the alert. Unfortunately OpenSSL mishandled this alert and would hang
waiting for a server hello which it will never receive. Now we treat a
received no_renegotiation alert as a fatal error. This is because
applications requesting a renegotiation might well expect it to succeed
and would have no code in place to handle the server denying it so the
only safe thing to do is to terminate the connection.
[Steve Henson]
*) Add ctrl macro SSL_get_secure_renegotiation_support() which returns 1 if
peer supports secure renegotiation and 0 otherwise. Print out peer
renegotiation support in s_client/s_server.
[Steve Henson]
*) Replace the highly broken and deprecated SPKAC certification method with
the updated NID creation version. This should correctly handle UTF8.
[Steve Henson]
*) Implement RFC5746. Re-enable renegotiation but require the extension
as needed. Unfortunately, SSL3_FLAGS_ALLOW_UNSAFE_LEGACY_RENEGOTIATION
turns out to be a bad idea. It has been replaced by
SSL_OP_ALLOW_UNSAFE_LEGACY_RENEGOTIATION which can be set with
SSL_CTX_set_options(). This is really not recommended unless you
know what you are doing.
[Eric Rescorla <ekr@networkresonance.com>, Ben Laurie, Steve Henson]
*) Fixes to stateless session resumption handling. Use initial_ctx when
issuing and attempting to decrypt tickets in case it has changed during
servername handling. Use a non-zero length session ID when attempting
stateless session resumption: this makes it possible to determine if
a resumption has occurred immediately after receiving server hello
(several places in OpenSSL subtly assume this) instead of later in
the handshake.
[Steve Henson]
*) The functions ENGINE_ctrl(), OPENSSL_isservice(),
CMS_get1_RecipientRequest() and RAND_bytes() can return <=0 on error
fixes for a few places where the return code is not checked
correctly.
[Julia Lawall <julia@diku.dk>]
*) Add --strict-warnings option to Configure script to include devteam
warnings in other configurations.
[Steve Henson]
*) Add support for --libdir option and LIBDIR variable in makefiles. This
makes it possible to install openssl libraries in locations which
have names other than "lib", for example "/usr/lib64" which some
systems need.
[Steve Henson, based on patch from Jeremy Utley]
*) Don't allow the use of leading 0x80 in OIDs. This is a violation of
X690 8.9.12 and can produce some misleading textual output of OIDs.
[Steve Henson, reported by Dan Kaminsky]
*) Delete MD2 from algorithm tables. This follows the recommendation in
several standards that it is not used in new applications due to
several cryptographic weaknesses. For binary compatibility reasons
the MD2 API is still compiled in by default.
[Steve Henson]
*) Add compression id to {d2i,i2d}_SSL_SESSION so it is correctly saved
and restored.
[Steve Henson]
*) Rename uni2asc and asc2uni functions to OPENSSL_uni2asc and
OPENSSL_asc2uni conditionally on Netware platforms to avoid a name
clash.
[Guenter <lists@gknw.net>]
*) Fix the server certificate chain building code to use X509_verify_cert(),
it used to have an ad-hoc builder which was unable to cope with anything
other than a simple chain.
[David Woodhouse <dwmw2@infradead.org>, Steve Henson]
*) Don't check self signed certificate signatures in X509_verify_cert()
by default (a flag can override this): it just wastes time without
adding any security. As a useful side effect self signed root CAs
with non-FIPS digests are now usable in FIPS mode.
[Steve Henson]
*) In dtls1_process_out_of_seq_message() the check if the current message
is already buffered was missing. For every new message was memory
allocated, allowing an attacker to perform an denial of service attack
with sending out of seq handshake messages until there is no memory
left. Additionally every future messege was buffered, even if the
sequence number made no sense and would be part of another handshake.
So only messages with sequence numbers less than 10 in advance will be
buffered. (CVE-2009-1378)
[Robin Seggelmann, discovered by Daniel Mentz]
*) Records are buffered if they arrive with a future epoch to be
processed after finishing the corresponding handshake. There is
currently no limitation to this buffer allowing an attacker to perform
a DOS attack with sending records with future epochs until there is no
memory left. This patch adds the pqueue_size() function to detemine
the size of a buffer and limits the record buffer to 100 entries.
(CVE-2009-1377)
[Robin Seggelmann, discovered by Daniel Mentz]
*) Keep a copy of frag->msg_header.frag_len so it can be used after the
parent structure is freed. (CVE-2009-1379)
[Daniel Mentz]
*) Handle non-blocking I/O properly in SSL_shutdown() call.
[Darryl Miles <darryl-mailinglists@netbauds.net>]
*) Add 2.5.4.* OIDs
[Ilya O. <vrghost@gmail.com>] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8m-os2knix-20100228-dev.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8m-os2knix-20100228-dev.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8m (runtime, 28/2/2010) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8l and 0.9.8m [25 Feb 2010]
*) Always check bn_wexpend() return values for failure. (CVE-2009-3245)
[Martin Olsson, Neel Mehta]
*) Fix X509_STORE locking: Every 'objs' access requires a lock (to
accommodate for stack sorting, always a write lock!).
[Bodo Moeller]
*) On some versions of WIN32 Heap32Next is very slow. This can cause
excessive delays in the RAND_poll(): over a minute. As a workaround
include a time check in the inner Heap32Next loop too.
[Steve Henson]
*) The code that handled flushing of data in SSL/TLS originally used the
BIO_CTRL_INFO ctrl to see if any data was pending first. This caused
the problem outlined in PR#1949. The fix suggested there however can
trigger problems with buggy BIO_CTRL_WPENDING (e.g. some versions
of Apache). So instead simplify the code to flush unconditionally.
This should be fine since flushing with no data to flush is a no op.
[Steve Henson]
*) Handle TLS versions 2.0 and later properly and correctly use the
highest version of TLS/SSL supported. Although TLS >= 2.0 is some way
off ancient servers have a habit of sticking around for a while...
[Steve Henson]
*) Modify compression code so it frees up structures without using the
ex_data callbacks. This works around a problem where some applications
call CRYPTO_cleanup_all_ex_data() before application exit (e.g. when
restarting) then use compression (e.g. SSL with compression) later.
This results in significant per-connection memory leaks and
has caused some security issues including CVE-2008-1678 and
CVE-2009-4355.
[Steve Henson]
*) Constify crypto/cast (i.e., <openssl/cast.h>): a CAST_KEY doesn't
change when encrypting or decrypting.
[Bodo Moeller]
*) Add option SSL_OP_LEGACY_SERVER_CONNECT which will allow clients to
connect and renegotiate with servers which do not support RI.
Until RI is more widely deployed this option is enabled by default.
[Steve Henson]
*) Add "missing" ssl ctrls to clear options and mode.
[Steve Henson]
*) If client attempts to renegotiate and doesn't support RI respond with
a no_renegotiation alert as required by RFC5746. Some renegotiating
TLS clients will continue a connection gracefully when they receive
the alert. Unfortunately OpenSSL mishandled this alert and would hang
waiting for a server hello which it will never receive. Now we treat a
received no_renegotiation alert as a fatal error. This is because
applications requesting a renegotiation might well expect it to succeed
and would have no code in place to handle the server denying it so the
only safe thing to do is to terminate the connection.
[Steve Henson]
*) Add ctrl macro SSL_get_secure_renegotiation_support() which returns 1 if
peer supports secure renegotiation and 0 otherwise. Print out peer
renegotiation support in s_client/s_server.
[Steve Henson]
*) Replace the highly broken and deprecated SPKAC certification method with
the updated NID creation version. This should correctly handle UTF8.
[Steve Henson]
*) Implement RFC5746. Re-enable renegotiation but require the extension
as needed. Unfortunately, SSL3_FLAGS_ALLOW_UNSAFE_LEGACY_RENEGOTIATION
turns out to be a bad idea. It has been replaced by
SSL_OP_ALLOW_UNSAFE_LEGACY_RENEGOTIATION which can be set with
SSL_CTX_set_options(). This is really not recommended unless you
know what you are doing.
[Eric Rescorla <ekr@networkresonance.com>, Ben Laurie, Steve Henson]
*) Fixes to stateless session resumption handling. Use initial_ctx when
issuing and attempting to decrypt tickets in case it has changed during
servername handling. Use a non-zero length session ID when attempting
stateless session resumption: this makes it possible to determine if
a resumption has occurred immediately after receiving server hello
(several places in OpenSSL subtly assume this) instead of later in
the handshake.
[Steve Henson]
*) The functions ENGINE_ctrl(), OPENSSL_isservice(),
CMS_get1_RecipientRequest() and RAND_bytes() can return <=0 on error
fixes for a few places where the return code is not checked
correctly.
[Julia Lawall <julia@diku.dk>]
*) Add --strict-warnings option to Configure script to include devteam
warnings in other configurations.
[Steve Henson]
*) Add support for --libdir option and LIBDIR variable in makefiles. This
makes it possible to install openssl libraries in locations which
have names other than "lib", for example "/usr/lib64" which some
systems need.
[Steve Henson, based on patch from Jeremy Utley]
*) Don't allow the use of leading 0x80 in OIDs. This is a violation of
X690 8.9.12 and can produce some misleading textual output of OIDs.
[Steve Henson, reported by Dan Kaminsky]
*) Delete MD2 from algorithm tables. This follows the recommendation in
several standards that it is not used in new applications due to
several cryptographic weaknesses. For binary compatibility reasons
the MD2 API is still compiled in by default.
[Steve Henson]
*) Add compression id to {d2i,i2d}_SSL_SESSION so it is correctly saved
and restored.
[Steve Henson]
*) Rename uni2asc and asc2uni functions to OPENSSL_uni2asc and
OPENSSL_asc2uni conditionally on Netware platforms to avoid a name
clash.
[Guenter <lists@gknw.net>]
*) Fix the server certificate chain building code to use X509_verify_cert(),
it used to have an ad-hoc builder which was unable to cope with anything
other than a simple chain.
[David Woodhouse <dwmw2@infradead.org>, Steve Henson]
*) Don't check self signed certificate signatures in X509_verify_cert()
by default (a flag can override this): it just wastes time without
adding any security. As a useful side effect self signed root CAs
with non-FIPS digests are now usable in FIPS mode.
[Steve Henson]
*) In dtls1_process_out_of_seq_message() the check if the current message
is already buffered was missing. For every new message was memory
allocated, allowing an attacker to perform an denial of service attack
with sending out of seq handshake messages until there is no memory
left. Additionally every future messege was buffered, even if the
sequence number made no sense and would be part of another handshake.
So only messages with sequence numbers less than 10 in advance will be
buffered. (CVE-2009-1378)
[Robin Seggelmann, discovered by Daniel Mentz]
*) Records are buffered if they arrive with a future epoch to be
processed after finishing the corresponding handshake. There is
currently no limitation to this buffer allowing an attacker to perform
a DOS attack with sending records with future epochs until there is no
memory left. This patch adds the pqueue_size() function to detemine
the size of a buffer and limits the record buffer to 100 entries.
(CVE-2009-1377)
[Robin Seggelmann, discovered by Daniel Mentz]
*) Keep a copy of frag->msg_header.frag_len so it can be used after the
parent structure is freed. (CVE-2009-1379)
[Daniel Mentz]
*) Handle non-blocking I/O properly in SSL_shutdown() call.
[Darryl Miles <darryl-mailinglists@netbauds.net>]
*) Add 2.5.4.* OIDs
[Ilya O. <vrghost@gmail.com>] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8m-os2knix-20100228-runtime.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8m-os2knix-20100228-runtime.zip |
 local copy local copy
|
|
OpenSSL v. 1.0.0b3 (20/9/2009, Paul Smedley (Smedles)) |
|
|
 www.os2site.com/sw/internet/openssl/old/openssl-1.0.0-beta3-os2.zip www.os2site.com/sw/internet/openssl/old/openssl-1.0.0-beta3-os2.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8j (klibc, 15/1/2009) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8i and 0.9.8j [07 Jan 2009]
*) Properly check EVP_VerifyFinal() and similar return values
(CVE-2008-5077).
[Ben Laurie, Bodo Moeller, Google Security Team]
*) Properly check EVP_VerifyFinal() and similar return values
(CVE-2008-5077).
[Ben Laurie, Bodo Moeller, Google Security Team]
*) Enable TLS extensions by default.
[Ben Laurie]
*) Allow the CHIL engine to be loaded, whether the application is
multithreaded or not. (This does not release the developer from the
obligation to set up the dynamic locking callbacks.)
[Sander Temme <sander@temme.net>]
*) Use correct exit code if there is an error in dgst command.
[Steve Henson; problem pointed out by Roland Dirlewanger]
*) Tweak Configure so that you need to say "experimental-jpake" to enable
JPAKE, and need to use -DOPENSSL_EXPERIMENTAL_JPAKE in applications.
[Bodo Moeller]
*) Add experimental JPAKE support, including demo authentication in
s_client and s_server.
[Ben Laurie]
*) Set the comparison function in v3_addr_canonize().
[Rob Austein <sra@hactrn.net>]
*) Add support for XMPP STARTTLS in s_client.
[Philip Paeps <philip@freebsd.org>]
*) Change the server-side SSL_OP_NETSCAPE_REUSE_CIPHER_CHANGE_BUG behavior
to ensure that even with this option, only ciphersuites in the
server's preference list will be accepted. (Note that the option
applies only when resuming a session, so the earlier behavior was
just about the algorithm choice for symmetric cryptography.)
[Bodo Moeller] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8j-klibc-gcc432-20090115.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8j-klibc-gcc432-20090115.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8j (emx, 15/1/2009) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8i and 0.9.8j [07 Jan 2009]
*) Properly check EVP_VerifyFinal() and similar return values
(CVE-2008-5077).
[Ben Laurie, Bodo Moeller, Google Security Team]
*) Properly check EVP_VerifyFinal() and similar return values
(CVE-2008-5077).
[Ben Laurie, Bodo Moeller, Google Security Team]
*) Enable TLS extensions by default.
[Ben Laurie]
*) Allow the CHIL engine to be loaded, whether the application is
multithreaded or not. (This does not release the developer from the
obligation to set up the dynamic locking callbacks.)
[Sander Temme <sander@temme.net>]
*) Use correct exit code if there is an error in dgst command.
[Steve Henson; problem pointed out by Roland Dirlewanger]
*) Tweak Configure so that you need to say "experimental-jpake" to enable
JPAKE, and need to use -DOPENSSL_EXPERIMENTAL_JPAKE in applications.
[Bodo Moeller]
*) Add experimental JPAKE support, including demo authentication in
s_client and s_server.
[Ben Laurie]
*) Set the comparison function in v3_addr_canonize().
[Rob Austein <sra@hactrn.net>]
*) Add support for XMPP STARTTLS in s_client.
[Philip Paeps <philip@freebsd.org>]
*) Change the server-side SSL_OP_NETSCAPE_REUSE_CIPHER_CHANGE_BUG behavior
to ensure that even with this option, only ciphersuites in the
server's preference list will be accepted. (Note that the option
applies only when resuming a session, so the earlier behavior was
just about the algorithm choice for symmetric cryptography.)
[Bodo Moeller] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8j-os2emx-20090115.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8j-os2emx-20090115.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8i (18/9/2008) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8h and 0.9.8i [15 Sep 2008]
*) Fix a state transitition in s3_srvr.c and d1_srvr.c
(was using SSL3_ST_CW_CLNT_HELLO_B, should be ..._ST_SW_SRVR_...).
[Nagendra Modadugu]
*) The fix in 0.9.8c that supposedly got rid of unsafe
double-checked locking was incomplete for RSA blinding,
addressing just one layer of what turns out to have been
doubly unsafe triple-checked locking.
So now fix this for real by retiring the MONT_HELPER macro
in crypto/rsa/rsa_eay.c.
[Bodo Moeller; problem pointed out by Marius Schilder]
*) Various precautionary measures:
- Avoid size_t integer overflow in HASH_UPDATE (md32_common.h).
- Avoid a buffer overflow in d2i_SSL_SESSION() (ssl_asn1.c).
(NB: This would require knowledge of the secret session ticket key
to exploit, in which case you'd be SOL either way.)
- Change bn_nist.c so that it will properly handle input BIGNUMs
outside the expected range.
- Enforce the 'num' check in BN_div() (bn_div.c) for non-BN_DEBUG
builds.
[Neel Mehta, Bodo Moeller]
*) Add support for Local Machine Keyset attribute in PKCS#12 files.
[Steve Henson]
*) Fix BN_GF2m_mod_arr() top-bit cleanup code.
[Huang Ying]
*) Expand ENGINE to support engine supplied SSL client certificate functions.
This work was sponsored by Logica.
[Steve Henson]
*) Add CryptoAPI ENGINE to support use of RSA and DSA keys held in Windows
keystores. Support for SSL/TLS client authentication too.
Not compiled unless enable-capieng specified to Configure.
This work was sponsored by Logica.
[Steve Henson]
*) Allow engines to be "soft loaded" - i.e. optionally don't die if
the load fails. Useful for distros.
[Ben Laurie and the FreeBSD team] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8i-klibc-20080918.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8i-klibc-20080918.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8h (emx, 30/5/2008) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8g and 0.9.8h [28 May 2008]
*) Fix flaw if 'Server Key exchange message' is omitted from a TLS
handshake which could lead to a cilent crash as found using the
Codenomicon TLS test suite (CVE-2008-1672)
[Steve Henson, Mark Cox]
*) Fix double free in TLS server name extensions which could lead to
a remote crash found by Codenomicon TLS test suite (CVE-2008-0891)
[Joe Orton]
*) Clear error queue in SSL_CTX_use_certificate_chain_file()
Clear the error queue to ensure that error entries left from
older function calls do not interfere with the correct operation.
[Lutz Jaenicke, Erik de Castro Lopo]
*) Remove root CA certificates of commercial CAs:
The OpenSSL project does not recommend any specific CA and does not
have any policy with respect to including or excluding any CA.
Therefore it does not make any sense to ship an arbitrary selection
of root CA certificates with the OpenSSL software.
[Lutz Jaenicke]
*) RSA OAEP patches to fix two separate invalid memory reads.
The first one involves inputs when 'lzero' is greater than
'SHA_DIGEST_LENGTH' (it would read about SHA_DIGEST_LENGTH bytes
before the beginning of from). The second one involves inputs where
the 'db' section contains nothing but zeroes (there is a one-byte
invalid read after the end of 'db').
[Ivan Nestlerode <inestlerode@us.ibm.com>]
*) Partial backport from 0.9.9-dev:
Introduce bn_mul_mont (dedicated Montgomery multiplication
procedure) as a candidate for BIGNUM assembler implementation.
While 0.9.9-dev uses assembler for various architectures, only
x86_64 is available by default here in the 0.9.8 branch, and
32-bit x86 is available through a compile-time setting.
To try the 32-bit x86 assembler implementation, use Configure
option "enable-montasm" (which exists only for this backport).
As "enable-montasm" for 32-bit x86 disclaims code stability
anyway, in this constellation we activate additional code
backported from 0.9.9-dev for further performance improvements,
namely BN_from_montgomery_word. (To enable this otherwise,
e.g. x86_64, try "-DMONT_FROM_WORD___NON_DEFAULT_0_9_8_BUILD".)
[Andy Polyakov (backport partially by Bodo Moeller)]
*) Add TLS session ticket callback. This allows an application to set
TLS ticket cipher and HMAC keys rather than relying on hardcoded fixed
values. This is useful for key rollover for example where several key
sets may exist with different names.
[Steve Henson]
*) Reverse ENGINE-internal logic for caching default ENGINE handles.
This was broken until now in 0.9.8 releases, such that the only way
a registered ENGINE could be used (assuming it initialises
successfully on the host) was to explicitly set it as the default
for the relevant algorithms. This is in contradiction with 0.9.7
behaviour and the documentation. With this fix, when an ENGINE is
registered into a given algorithm's table of implementations, the
'uptodate' flag is reset so that auto-discovery will be used next
time a new context for that algorithm attempts to select an
implementation.
[Ian Lister (tweaked by Geoff Thorpe)]
*) Backport of CMS code to OpenSSL 0.9.8. This differs from the 0.9.9
implemention in the following ways:
Lack of EVP_PKEY_ASN1_METHOD means algorithm parameters have to be
hard coded.
Lack of BER streaming support means one pass streaming processing is
only supported if data is detached: setting the streaming flag is
ignored for embedded content.
CMS support is disabled by default and must be explicitly enabled
with the enable-cms configuration option.
[Steve Henson]
*) Update the GMP engine glue to do direct copies between BIGNUM and
mpz_t when openssl and GMP use the same limb size. Otherwise the
existing "conversion via a text string export" trick is still used.
[Paul Sheer <paulsheer@gmail.com>]
*) Zlib compression BIO. This is a filter BIO which compressed and
uncompresses any data passed through it.
[Steve Henson]
*) Add AES_wrap_key() and AES_unwrap_key() functions to implement
RFC3394 compatible AES key wrapping.
[Steve Henson]
*) Add utility functions to handle ASN1 structures. ASN1_STRING_set0():
sets string data without copying. X509_ALGOR_set0() and
X509_ALGOR_get0(): set and retrieve X509_ALGOR (AlgorithmIdentifier)
data. Attribute function X509at_get0_data_by_OBJ(): retrieves data
from an X509_ATTRIBUTE structure optionally checking it occurs only
once. ASN1_TYPE_set1(): set and ASN1_TYPE structure copying supplied
data.
[Steve Henson]
*) Fix BN flag handling in RSA_eay_mod_exp() and BN_MONT_CTX_set()
to get the expected BN_FLG_CONSTTIME behavior.
[Bodo Moeller (Google)]
*) Netware support:
- fixed wrong usage of ioctlsocket() when build for LIBC BSD sockets
- fixed do_tests.pl to run the test suite with CLIB builds too (CLIB_OPT)
- added some more tests to do_tests.pl
- fixed RunningProcess usage so that it works with newer LIBC NDKs too
- removed usage of BN_LLONG for CLIB builds to avoid runtime dependency
- added new Configure targets netware-clib-bsdsock, netware-clib-gcc,
netware-clib-bsdsock-gcc, netware-libc-bsdsock-gcc
- various changes to netware.pl to enable gcc-cross builds on Win32
platform
- changed crypto/bio/b_sock.c to work with macro functions (CLIB BSD)
- various changes to fix missing prototype warnings
- fixed x86nasm.pl to create correct asm files for NASM COFF output
- added AES, WHIRLPOOL and CPUID assembler code to build files
- added missing AES assembler make rules to mk1mf.pl
- fixed order of includes in apps/ocsp.c so that e_os.h settings apply
[Guenter Knauf <eflash@gmx.net>]
*) Implement certificate status request TLS extension defined in RFC3546.
A client can set the appropriate parameters and receive the encoded
OCSP response via a callback. A server can query the supplied parameters
and set the encoded OCSP response in the callback. Add simplified examples
to s_client and s_server.
[Steve Henson] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8h-os2emx-20080530.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8h-os2emx-20080530.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8h (klibc, 30/5/2008) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8g and 0.9.8h [28 May 2008]
*) Fix flaw if 'Server Key exchange message' is omitted from a TLS
handshake which could lead to a cilent crash as found using the
Codenomicon TLS test suite (CVE-2008-1672)
[Steve Henson, Mark Cox]
*) Fix double free in TLS server name extensions which could lead to
a remote crash found by Codenomicon TLS test suite (CVE-2008-0891)
[Joe Orton]
*) Clear error queue in SSL_CTX_use_certificate_chain_file()
Clear the error queue to ensure that error entries left from
older function calls do not interfere with the correct operation.
[Lutz Jaenicke, Erik de Castro Lopo]
*) Remove root CA certificates of commercial CAs:
The OpenSSL project does not recommend any specific CA and does not
have any policy with respect to including or excluding any CA.
Therefore it does not make any sense to ship an arbitrary selection
of root CA certificates with the OpenSSL software.
[Lutz Jaenicke]
*) RSA OAEP patches to fix two separate invalid memory reads.
The first one involves inputs when 'lzero' is greater than
'SHA_DIGEST_LENGTH' (it would read about SHA_DIGEST_LENGTH bytes
before the beginning of from). The second one involves inputs where
the 'db' section contains nothing but zeroes (there is a one-byte
invalid read after the end of 'db').
[Ivan Nestlerode <inestlerode@us.ibm.com>]
*) Partial backport from 0.9.9-dev:
Introduce bn_mul_mont (dedicated Montgomery multiplication
procedure) as a candidate for BIGNUM assembler implementation.
While 0.9.9-dev uses assembler for various architectures, only
x86_64 is available by default here in the 0.9.8 branch, and
32-bit x86 is available through a compile-time setting.
To try the 32-bit x86 assembler implementation, use Configure
option "enable-montasm" (which exists only for this backport).
As "enable-montasm" for 32-bit x86 disclaims code stability
anyway, in this constellation we activate additional code
backported from 0.9.9-dev for further performance improvements,
namely BN_from_montgomery_word. (To enable this otherwise,
e.g. x86_64, try "-DMONT_FROM_WORD___NON_DEFAULT_0_9_8_BUILD".)
[Andy Polyakov (backport partially by Bodo Moeller)]
*) Add TLS session ticket callback. This allows an application to set
TLS ticket cipher and HMAC keys rather than relying on hardcoded fixed
values. This is useful for key rollover for example where several key
sets may exist with different names.
[Steve Henson]
*) Reverse ENGINE-internal logic for caching default ENGINE handles.
This was broken until now in 0.9.8 releases, such that the only way
a registered ENGINE could be used (assuming it initialises
successfully on the host) was to explicitly set it as the default
for the relevant algorithms. This is in contradiction with 0.9.7
behaviour and the documentation. With this fix, when an ENGINE is
registered into a given algorithm's table of implementations, the
'uptodate' flag is reset so that auto-discovery will be used next
time a new context for that algorithm attempts to select an
implementation.
[Ian Lister (tweaked by Geoff Thorpe)]
*) Backport of CMS code to OpenSSL 0.9.8. This differs from the 0.9.9
implemention in the following ways:
Lack of EVP_PKEY_ASN1_METHOD means algorithm parameters have to be
hard coded.
Lack of BER streaming support means one pass streaming processing is
only supported if data is detached: setting the streaming flag is
ignored for embedded content.
CMS support is disabled by default and must be explicitly enabled
with the enable-cms configuration option.
[Steve Henson]
*) Update the GMP engine glue to do direct copies between BIGNUM and
mpz_t when openssl and GMP use the same limb size. Otherwise the
existing "conversion via a text string export" trick is still used.
[Paul Sheer <paulsheer@gmail.com>]
*) Zlib compression BIO. This is a filter BIO which compressed and
uncompresses any data passed through it.
[Steve Henson]
*) Add AES_wrap_key() and AES_unwrap_key() functions to implement
RFC3394 compatible AES key wrapping.
[Steve Henson]
*) Add utility functions to handle ASN1 structures. ASN1_STRING_set0():
sets string data without copying. X509_ALGOR_set0() and
X509_ALGOR_get0(): set and retrieve X509_ALGOR (AlgorithmIdentifier)
data. Attribute function X509at_get0_data_by_OBJ(): retrieves data
from an X509_ATTRIBUTE structure optionally checking it occurs only
once. ASN1_TYPE_set1(): set and ASN1_TYPE structure copying supplied
data.
[Steve Henson]
*) Fix BN flag handling in RSA_eay_mod_exp() and BN_MONT_CTX_set()
to get the expected BN_FLG_CONSTTIME behavior.
[Bodo Moeller (Google)]
*) Netware support:
- fixed wrong usage of ioctlsocket() when build for LIBC BSD sockets
- fixed do_tests.pl to run the test suite with CLIB builds too (CLIB_OPT)
- added some more tests to do_tests.pl
- fixed RunningProcess usage so that it works with newer LIBC NDKs too
- removed usage of BN_LLONG for CLIB builds to avoid runtime dependency
- added new Configure targets netware-clib-bsdsock, netware-clib-gcc,
netware-clib-bsdsock-gcc, netware-libc-bsdsock-gcc
- various changes to netware.pl to enable gcc-cross builds on Win32
platform
- changed crypto/bio/b_sock.c to work with macro functions (CLIB BSD)
- various changes to fix missing prototype warnings
- fixed x86nasm.pl to create correct asm files for NASM COFF output
- added AES, WHIRLPOOL and CPUID assembler code to build files
- added missing AES assembler make rules to mk1mf.pl
- fixed order of includes in apps/ocsp.c so that e_os.h settings apply
[Guenter Knauf <eflash@gmx.net>]
*) Implement certificate status request TLS extension defined in RFC3546.
A client can set the appropriate parameters and receive the encoded
OCSP response via a callback. A server can query the supplied parameters
and set the encoded OCSP response in the callback. Add simplified examples
to s_client and s_server.
[Steve Henson] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8h-klibc-20080530.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8h-klibc-20080530.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8g (22/10/2007) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8f and 0.9.8g [19 Oct 2007]
*) Fix various bugs:
+ Binary incompatibility of ssl_ctx_st structure
+ DTLS interoperation with non-compliant servers
+ Don't call get_session_cb() without proposed session
+ Fix ia64 assembler code
[Andy Polyakov, Steve Henson] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8g-os2emx-20071022.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8g-os2emx-20071022.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8f (13/10/2007) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8e and 0.9.8f [11 Oct 2007]
*) DTLS Handshake overhaul. There were longstanding issues with
OpenSSL DTLS implementation, which were making it impossible for
RFC 4347 compliant client to communicate with OpenSSL server.
Unfortunately just fixing these incompatibilities would "cut off"
pre-0.9.8f clients. To allow for hassle free upgrade post-0.9.8e
server keeps tolerating non RFC compliant syntax. The opposite is
not true, 0.9.8f client can not communicate with earlier server.
This update even addresses CVE-2007-4995.
[Andy Polyakov]
*) Changes to avoid need for function casts in OpenSSL: some compilers
(gcc 4.2 and later) reject their use.
[Kurt Roeckx <kurt@roeckx.be>, Peter Hartley <pdh@utter.chaos.org.uk>,
Steve Henson]
*) Add RFC4507 support to OpenSSL. This includes the corrections in
RFC4507bis. The encrypted ticket format is an encrypted encoded
SSL_SESSION structure, that way new session features are automatically
supported.
If a client application caches session in an SSL_SESSION structure
support is transparent because tickets are now stored in the encoded
SSL_SESSION.
The SSL_CTX structure automatically generates keys for ticket
protection in servers so again support should be possible
with no application modification.
If a client or server wishes to disable RFC4507 support then the option
SSL_OP_NO_TICKET can be set.
Add a TLS extension debugging callback to allow the contents of any client
or server extensions to be examined.
This work was sponsored by Google.
[Steve Henson]
*) Add initial support for TLS extensions, specifically for the server_name
extension so far. The SSL_SESSION, SSL_CTX, and SSL data structures now
have new members for a host name. The SSL data structure has an
additional member SSL_CTX *initial_ctx so that new sessions can be
stored in that context to allow for session resumption, even after the
SSL has been switched to a new SSL_CTX in reaction to a client's
server_name extension.
New functions (subject to change):
SSL_get_servername()
SSL_get_servername_type()
SSL_set_SSL_CTX()
New CTRL codes and macros (subject to change):
SSL_CTRL_SET_TLSEXT_SERVERNAME_CB
- SSL_CTX_set_tlsext_servername_callback()
SSL_CTRL_SET_TLSEXT_SERVERNAME_ARG
- SSL_CTX_set_tlsext_servername_arg()
SSL_CTRL_SET_TLSEXT_HOSTNAME - SSL_set_tlsext_host_name()
openssl s_client has a new '-servername ...' option.
openssl s_server has new options '-servername_host ...', '-cert2 ...',
'-key2 ...', '-servername_fatal' (subject to change). This allows
testing the HostName extension for a specific single host name ('-cert'
and '-key' remain fallbacks for handshakes without HostName
negotiation). If the unrecogninzed_name alert has to be sent, this by
default is a warning; it becomes fatal with the '-servername_fatal'
option.
[Peter Sylvester, Remy Allais, Christophe Renou, Steve Henson]
*) Add AES and SSE2 assembly language support to VC++ build.
[Steve Henson]
*) Mitigate attack on final subtraction in Montgomery reduction.
[Andy Polyakov]
*) Fix crypto/ec/ec_mult.c to work properly with scalars of value 0
(which previously caused an internal error).
[Bodo Moeller]
*) Squeeze another 10% out of IGE mode when in != out.
[Ben Laurie]
*) AES IGE mode speedup.
[Dean Gaudet (Google)]
*) Add the Korean symmetric 128-bit cipher SEED (see
http://www.kisa.or.kr/kisa/seed/jsp/seed_eng.jsp) and
add SEED ciphersuites from RFC 4162:
TLS_RSA_WITH_SEED_CBC_SHA = "SEED-SHA"
TLS_DHE_DSS_WITH_SEED_CBC_SHA = "DHE-DSS-SEED-SHA"
TLS_DHE_RSA_WITH_SEED_CBC_SHA = "DHE-RSA-SEED-SHA"
TLS_DH_anon_WITH_SEED_CBC_SHA = "ADH-SEED-SHA"
To minimize changes between patchlevels in the OpenSSL 0.9.8
series, SEED remains excluded from compilation unless OpenSSL
is configured with 'enable-seed'.
[KISA, Bodo Moeller]
*) Mitigate branch prediction attacks, which can be practical if a
single processor is shared, allowing a spy process to extract
information. For detailed background information, see
http://eprint.iacr.org/2007/039 (O. Aciicmez, S. Gueron,
J.-P. Seifert, "New Branch Prediction Vulnerabilities in OpenSSL
and Necessary Software Countermeasures"). The core of the change
are new versions BN_div_no_branch() and
BN_mod_inverse_no_branch() of BN_div() and BN_mod_inverse(),
respectively, which are slower, but avoid the security-relevant
conditional branches. These are automatically called by BN_div()
and BN_mod_inverse() if the flag BN_FLG_CONSTTIME is set for one
of the input BIGNUMs. Also, BN_is_bit_set() has been changed to
remove a conditional branch.
BN_FLG_CONSTTIME is the new name for the previous
BN_FLG_EXP_CONSTTIME flag, since it now affects more than just
modular exponentiation. (Since OpenSSL 0.9.7h, setting this flag
in the exponent causes BN_mod_exp_mont() to use the alternative
implementation in BN_mod_exp_mont_consttime().) The old name
remains as a deprecated alias.
Similary, RSA_FLAG_NO_EXP_CONSTTIME is replaced by a more general
RSA_FLAG_NO_CONSTTIME flag since the RSA implementation now uses
constant-time implementations for more than just exponentiation.
Here too the old name is kept as a deprecated alias.
BN_BLINDING_new() will now use BN_dup() for the modulus so that
the BN_BLINDING structure gets an independent copy of the
modulus. This means that the previous "BIGNUM *m" argument to
BN_BLINDING_new() and to BN_BLINDING_create_param() now
essentially becomes "const BIGNUM *m", although we can't actually
change this in the header file before 0.9.9. It allows
RSA_setup_blinding() to use BN_with_flags() on the modulus to
enable BN_FLG_CONSTTIME.
[Matthew D Wood (Intel Corp)]
*) In the SSL/TLS server implementation, be strict about session ID
context matching (which matters if an application uses a single
external cache for different purposes). Previously,
out-of-context reuse was forbidden only if SSL_VERIFY_PEER was
set. This did ensure strict client verification, but meant that,
with applications using a single external cache for quite
different requirements, clients could circumvent ciphersuite
restrictions for a given session ID context by starting a session
in a different context.
[Bodo Moeller]
*) Include "!eNULL" in SSL_DEFAULT_CIPHER_LIST to make sure that
a ciphersuite string such as "DEFAULT:RSA" cannot enable
authentication-only ciphersuites.
[Bodo Moeller] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8f-os2emx-20071013.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8f-os2emx-20071013.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8e (18/4/2007) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8d and 0.9.8e [23 Feb 2007]
*) Include "!eNULL" in SSL_DEFAULT_CIPHER_LIST to make sure that
a ciphersuite string such as "DEFAULT:RSA" cannot enable
authentication-only ciphersuites.
[Bodo Moeller]
*) Since AES128 and AES256 (and similarly Camellia128 and
Camellia256) share a single mask bit in the logic of
ssl/ssl_ciph.c, the code for masking out disabled ciphers needs a
kludge to work properly if AES128 is available and AES256 isn't
(or if Camellia128 is available and Camellia256 isn't).
[Victor Duchovni]
*) Fix the BIT STRING encoding generated by crypto/ec/ec_asn1.c
(within i2d_ECPrivateKey, i2d_ECPKParameters, i2d_ECParameters):
When a point or a seed is encoded in a BIT STRING, we need to
prevent the removal of trailing zero bits to get the proper DER
encoding. (By default, crypto/asn1/a_bitstr.c assumes the case
of a NamedBitList, for which trailing 0 bits need to be removed.)
[Bodo Moeller]
*) Have SSL/TLS server implementation tolerate "mismatched" record
protocol version while receiving ClientHello even if the
ClientHello is fragmented. (The server can't insist on the
particular protocol version it has chosen before the ServerHello
message has informed the client about his choice.)
[Bodo Moeller]
*) Add RFC 3779 support.
[Rob Austein for ARIN, Ben Laurie]
*) Load error codes if they are not already present instead of using a
static variable. This allows them to be cleanly unloaded and reloaded.
Improve header file function name parsing.
[Steve Henson]
*) extend SMTP and IMAP protocol emulation in s_client to use EHLO
or CAPABILITY handshake as required by RFCs.
[Goetz Babin-Ebell] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8e-os2-20070418.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8e-os2-20070418.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8d (29/9/2006) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8c and 0.9.8d [28 Sep 2006]
*) Introduce limits to prevent malicious keys being able to
cause a denial of service. (CVE-2006-2940)
[Steve Henson, Bodo Moeller]
*) Fix ASN.1 parsing of certain invalid structures that can result
in a denial of service. (CVE-2006-2937) [Steve Henson]
*) Fix buffer overflow in SSL_get_shared_ciphers() function.
(CVE-2006-3738) [Tavis Ormandy and Will Drewry, Google Security Team]
*) Fix SSL client code which could crash if connecting to a
malicious SSLv2 server. (CVE-2006-4343)
[Tavis Ormandy and Will Drewry, Google Security Team]
*) Since 0.9.8b, ciphersuite strings naming explicit ciphersuites
match only those. Before that, "AES256-SHA" would be interpreted
as a pattern and match "AES128-SHA" too (since AES128-SHA got
the same strength classification in 0.9.7h) as we currently only
have a single AES bit in the ciphersuite description bitmap.
That change, however, also applied to ciphersuite strings such as
"RC4-MD5" that intentionally matched multiple ciphersuites --
namely, SSL 2.0 ciphersuites in addition to the more common ones
from SSL 3.0/TLS 1.0.
So we change the selection algorithm again: Naming an explicit
ciphersuite selects this one ciphersuite, and any other similar
ciphersuite (same bitmap) from *other* protocol versions.
Thus, "RC4-MD5" again will properly select both the SSL 2.0
ciphersuite and the SSL 3.0/TLS 1.0 ciphersuite.
Since SSL 2.0 does not have any ciphersuites for which the
128/256 bit distinction would be relevant, this works for now.
The proper fix will be to use different bits for AES128 and
AES256, which would have avoided the problems from the beginning;
however, bits are scarce, so we can only do this in a new release
(not just a patchlevel) when we can change the SSL_CIPHER
definition to split the single 'unsigned long mask' bitmap into
multiple values to extend the available space.
[Bodo Moeller] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8d-os2-20060929.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8d-os2-20060929.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8c (7/9/2006) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8b and 0.9.8c [05 Sep 2006]
*) Avoid PKCS #1 v1.5 signature attack discovered by Daniel Bleichenbacher
(CVE-2006-4339) [Ben Laurie and Google Security Team]
*) Add AES IGE and biIGE modes.
[Ben Laurie]
*) Change the Unix randomness entropy gathering to use poll() when
possible instead of select(), since the latter has some
undesirable limitations.
[Darryl Miles via Richard Levitte and Bodo Moeller]
*) Disable "ECCdraft" ciphersuites more thoroughly. Now special
treatment in ssl/ssl_ciph.s makes sure that these ciphersuites
cannot be implicitly activated as part of, e.g., the "AES" alias.
However, please upgrade to OpenSSL 0.9.9[-dev] for
non-experimental use of the ECC ciphersuites to get TLS extension
support, which is required for curve and point format negotiation
to avoid potential handshake problems.
[Bodo Moeller]
*) Disable rogue ciphersuites:
- SSLv2 0x08 0x00 0x80 ("RC4-64-MD5")
- SSLv3/TLSv1 0x00 0x61 ("EXP1024-RC2-CBC-MD5")
- SSLv3/TLSv1 0x00 0x60 ("EXP1024-RC4-MD5")
The latter two were purportedly from
draft-ietf-tls-56-bit-ciphersuites-0[01].txt, but do not really
appear there.
Also deactive the remaining ciphersuites from
draft-ietf-tls-56-bit-ciphersuites-01.txt. These are just as
unofficial, and the ID has long expired.
[Bodo Moeller]
*) Fix RSA blinding Heisenbug (problems sometimes occured on
dual-core machines) and other potential thread-safety issues.
[Bodo Moeller]
*) Add the symmetric cipher Camellia (128-bit, 192-bit, 256-bit key
versions), which is now available for royalty-free use
(see http://info.isl.ntt.co.jp/crypt/eng/info/chiteki.html).
Also, add Camellia TLS ciphersuites from RFC 4132.
To minimize changes between patchlevels in the OpenSSL 0.9.8
series, Camellia remains excluded from compilation unless OpenSSL
is configured with 'enable-camellia'.
[NTT]
*) Disable the padding bug check when compression is in use. The padding
bug check assumes the first packet is of even length, this is not
necessarily true if compresssion is enabled and can result in false
positives causing handshake failure. The actual bug test is ancient
code so it is hoped that implementations will either have fixed it by
now or any which still have the bug do not support compression.
[Steve Henson] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8c-os2-20060907.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8c-os2-20060907.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8b (17/5/2006) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8a and 0.9.8b [04 May 2006]
*) When applying a cipher rule check to see if string match is an explicit
cipher suite and only match that one cipher suite if it is.
[Steve Henson]
*) Link in manifests for VC++ if needed.
[Austin Ziegler <halostatue@gmail.com>]
*) Update support for ECC-based TLS ciphersuites according to
draft-ietf-tls-ecc-12.txt with proposed changes (but without
TLS extensions, which are supported starting with the 0.9.9
branch, not in the OpenSSL 0.9.8 branch).
[Douglas Stebila]
*) New functions EVP_CIPHER_CTX_new() and EVP_CIPHER_CTX_free() to support
opaque EVP_CIPHER_CTX handling.
[Steve Henson]
*) Fixes and enhancements to zlib compression code. We now only use
"zlib1.dll" and use the default __cdecl calling convention on Win32
to conform with the standards mentioned here:
http://www.zlib.net/DLL_FAQ.txt
Static zlib linking now works on Windows and the new --with-zlib-include
--with-zlib-lib options to Configure can be used to supply the location
of the headers and library. Gracefully handle case where zlib library
can't be loaded.
[Steve Henson]
*) Several fixes and enhancements to the OID generation code. The old code
sometimes allowed invalid OIDs (1.X for X >= 40 for example), couldn't
handle numbers larger than ULONG_MAX, truncated printing and had a
non standard OBJ_obj2txt() behaviour.
[Steve Henson]
*) Add support for building of engines under engine/ as shared libraries
under VC++ build system.
[Steve Henson]
*) Corrected the numerous bugs in the Win32 path splitter in DSO.
Hopefully, we will not see any false combination of paths any more.
[Richard Levitte] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8b-os2-20060517.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8b-os2-20060517.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8a (13/11/2005) |
Readme/What's new |
OpenSSL CHANGES
_______________
Changes between 0.9.8 and 0.9.8a [11 Oct 2005]
*) Remove the functionality of SSL_OP_MSIE_SSLV2_RSA_PADDING
(part of SSL_OP_ALL). This option used to disable the
countermeasure against man-in-the-middle protocol-version
rollback in the SSL 2.0 server implementation, which is a bad
idea. (CAN-2005-2969)
[Bodo Moeller; problem pointed out by Yutaka Oiwa (Research Center
for Information Security, National Institute of Advanced Industrial
Science and Technology [AIST], Japan)]
*) Add two function to clear and return the verify parameter flags.
[Steve Henson]
*) Keep cipherlists sorted in the source instead of sorting them at
runtime, thus removing the need for a lock.
[Nils Larsch]
*) Avoid some small subgroup attacks in Diffie-Hellman.
[Nick Mathewson and Ben Laurie]
*) Add functions for well-known primes.
[Nick Mathewson]
*) Extended Windows CE support.
[Satoshi Nakamura and Andy Polyakov]
*) Initialize SSL_METHOD structures at compile time instead of during
runtime, thus removing the need for a lock.
[Steve Henson]
*) Make PKCS7_decrypt() work even if no certificate is supplied by
attempting to decrypt each encrypted key in turn. Add support to
smime utility.
[Steve Henson] |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8a-os2-20051113.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8a-os2-20051113.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.8 (3/8/2005, Yuri Dario (Paperino)) |
Readme/What's new |
Yuri Dario's build of OpenSSL v0.9.8 including full source tree with static libraries and binaries built with GCC v3.3.5. |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.8.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.8.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.7e (16/11/2004, Brian Havard) |
Readme/What's new |
Brian Havard's build of OpenSSL v0.9.7e. |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.7e-cli-os2.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.7e-cli-os2.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.7a (21/4/2003, Johannes Hromadka) |
Readme/What's new |
This is openssl-0.9.7a for OS/2. with the patch against the
Klima-Pokorny-Rosa attack on RSA in SSL/TLS applied.
I compiled it on Warp4 with emx 0.9d using OS2-EMX.cmd from
the original tar ball. The DLLs and EXE are compressed with LXLite.
Put openssl in a directory in your PATH and the DLLs to a direcotory
in your LIBPATH. Copy conf\openssl.cnf.demoCA to a directory of your
choice and set the environement variable OPENSSL_CONF by putting
SET OPENSSL_CONF=D:\MPTN\etc\ssl\openssl.cnf
into CONFIG.SYS.
If you want to compile your own programs and link them with
the opensll put the files from include and lib to your emx directory.
Note that openssl is a subdirectory of your include directory.
If you need .lib files you can create them using emxomf.
See the doc directory for some information and visit
http://www.columbia.edu/~ariel/ssleay/ for more infos.
Grab the full source at http://www.openssl.org/
There are many ways to make your own keys and certificates.
A good solution is to use sslRexx. It provides everithing you need
Here is a short desctription how I made my own Certification Authority,
a Server Key for Apache and a client Key/Certificate for me, signed by my
own CA.
Root CA: The root CA is needed to sign all certificates
=======
Generate a CA-Key and store it in sub-directory private:
openssl genrsa -des3 -out private/MyOwnCA.pem 2048
Make a selfsigned certificate based on above key.
openssl req -new -x509 -days 730 -key private/CAkey.pem -out CAcert.pem
optional generate text output of this certificate:
openssl x509 -in ./CAcert.pem -text > CAcert.txt
Now you have a key and certificate for your own CA which can be used
to sign user and server keys. The CAcert is also needed to configure
Apache and Netscape. You can/should give away the CA certificate but
never give the CA key to anybody.
Make a Key and Certificate for the Apache Server
================================================
Generate a key
--------------
openssl genrsa -des3 -out server-key.pem 2048
With this variant, you will be prompted for a protecting password. If
you don't want your key to be protected by a password, remove the flag
'-des3' from the command line above.
NOTE: if you intend to use the key together with a server
certificate, you may want to avoid protecting it with a password,
since that would mean someone would have to type in the password every
time the server needs to access the key. But then you should protect
the server key in another way.
Create a signing request
------------------------
openssl req -new -key server-key.pem -out server-req.pem
Now send this request to your CA for signing. Since you are your own CA
sign it:
--------
openssl ca -in server-req.pem -out server-cert.pem -outdir MyOwnCA/newcerts
Verify the certificate
openssl verify -CAfile CAcert.pem server-cert.pem
Now you have a key and a certificate for your Apache Webserver.
Your Client Certificate/Key
===========================
Generate a private key
----------------------
openssl genrsa -des3 -out hrom-key.pem 2048
Create a signing request
------------------------
openssl req -new -key hrom-key.pem -out hrom-req.pem
Let the CA sign it
------------------
openssl ca -in hrom-req.pem -out hrom-cert.pem -outdir MyOwnCA/newcerts
After you get back the certificate from the CA, combine it with
your private key and store the result as p12 file. This file can
be imported into your browser.
openssl pkcs12 -export -name Hromadka -in hrom-cert.pem -inkey hrom-key.pem -out hrom.p12
Securtiy Notes: Never give your private key to a CA, they only need the
signing request. Never give away your p12 file. Always secure your private
keys with a passphrase.
--
Johannes Hromadka
Johannes.Hromadka@gmx.net
2003-03-02 |
 hobbes.nmsu.edu/download/pub/os2/util/encrypt/openssl-0.9.7a-os2-bin.zip hobbes.nmsu.edu/download/pub/os2/util/encrypt/openssl-0.9.7a-os2-bin.zip |
|
|
OpenSSL v. 0.9.7d (21/3/2003, Brian Havard) |
Readme/What's new |
Brian Havard's build of OpenSSL v0.9.7d. |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.7d-cli-os2.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.7d-cli-os2.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.6 (15/2/2001, Vladimir Anufriev) |
Readme/What's new |
If you need to build the OpenSSL library for yourself, EG you're porting an application that requires SSL or other cryptography functions
provided by it, all you need to do is the following.
Download the official OpenSSL source code from the OpenSSL web site
Extract the source using tar xzf openssl-0.9.6.tar.gz
Delete all the 0 length files in openssl-0.9.6\include\openssl that tar makes in place of symlinks
Apply the patch openssl-emx.patch in the openssl-0.9.6 directory using a unix style patch program like gnupatch.zip and a command
line like patch -p0 < openssl-emx.patch
While still in the openssl-0.9.6 directory, run os2\emx.cmd to generate the makefiles. Note that this requires that you have a PERL
interpreter installed.
Run make -f emx.mak
Once finished, you'll find the libraries, test programs & the openssl.exe command line application in the out2 directory. You may need
to move the .a files up into the openssl-0.9.6 directory for other applications to find them for linking. |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.6.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.6.zip |
 local copy local copy
|
|
OpenSSL v. 0.9.6 (build on OS2, 3/2/2001, Ilya) |
Readme/What's new |
a) Needed to fix SHELL= lines in all the daughter Makefile.ssl files. Run
pfind -bak=-orig . "/^Makefile\.ssl$/" "=~ s/^(?=TOP\s*=)/SHELL=sh\n/"
and manually remove SHELL=/bin/sh from toplevel Makefile.ssl.
b) Add syslog.h to ./include; [I took it from ssh source of OS/2 port of 1.14]
c) Run make -f Makefile.ssl. When the build of openssl.exe fails,
put syslog.obj into the toplevel directory and run this:
cp os2/sslcrypt.def-short sslcrypt.def
cp os2/openssl.def-short openssl.def
emxexp libcrypto.a >>sslcrypt.def
emxexp libssl.a >>openssl.def
emxomf libcrypto.a libssl.a
emximp -o crypto.a sslcrypt.def
emximp -o ssl.a openssl.def
emximp -o crypto.lib sslcrypt.def
emximp -o ssl.lib openssl.def
gcc -Zmt -Zdll -Zomf -Zcrtdll -s -o sslcrypt.dll libcrypto.lib syslog.obj sslcrypt.def -lsocket
gcc -Zmt -Zdll -Zomf -Zcrtdll -s -o openssl.dll libssl.lib openssl.def -lsocket crypto.lib
make -f Makefile.ssl
to build tests and apps. Alternatively, apply the patch in
os2/patches/README and do as it is said there.
Problems:
1) openssl reads in text mode (See os2/patches/README for details);
2) not enough randomness;
3) A lot of test files hardwire /bin/rm; not all corrected.
Ilya |
 www.os2site.com/sw/internet/openssl/old/openssl-0.9.6-build-on-os2.zip www.os2site.com/sw/internet/openssl/old/openssl-0.9.6-build-on-os2.zip |
 local copy local copy
|


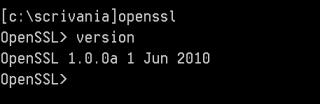


Aggiungi un commento